Reverse Engineering Nike Run Club Android App Using Frida - Yasoob Khalid
Por um escritor misterioso
Descrição
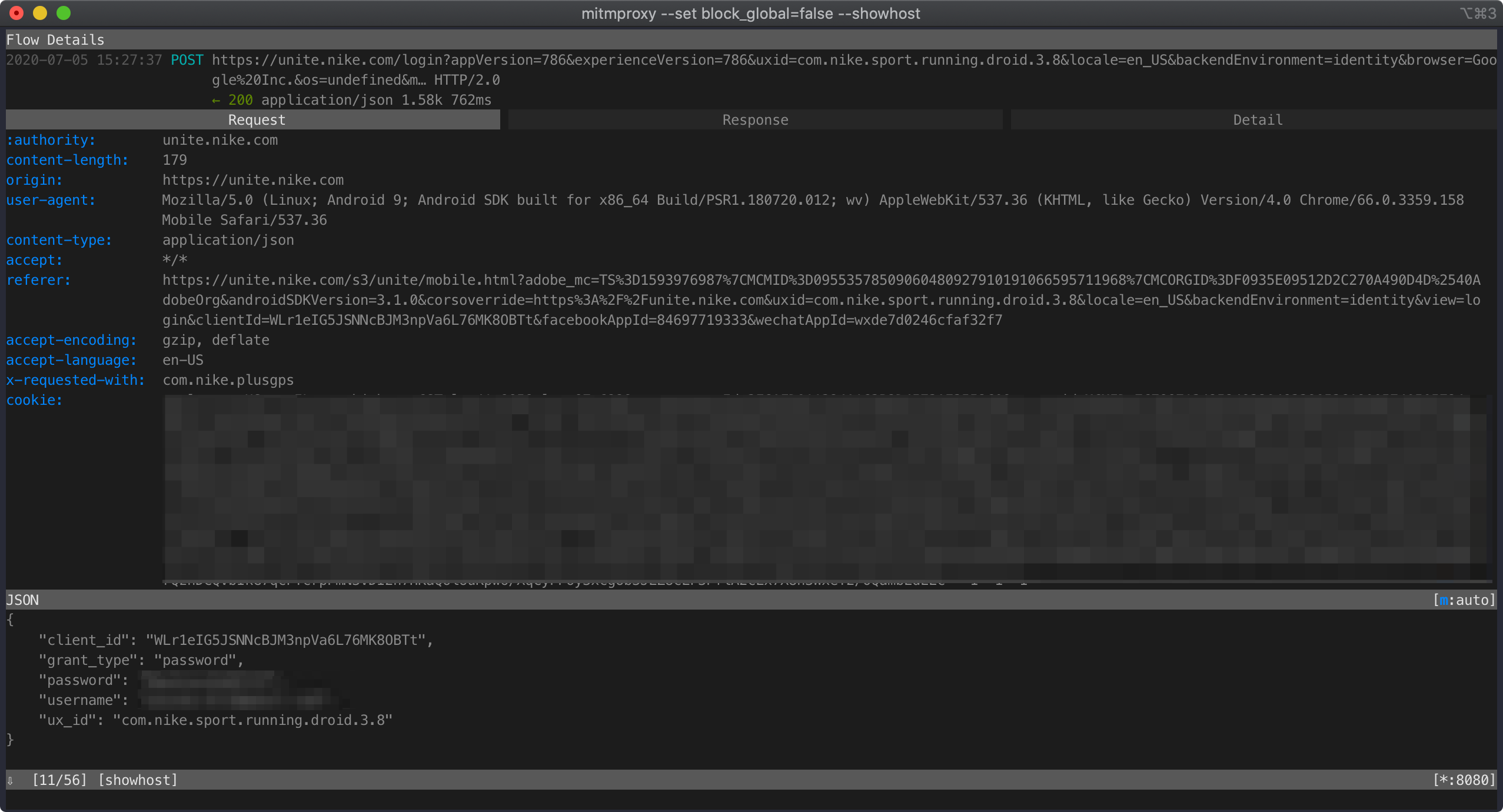
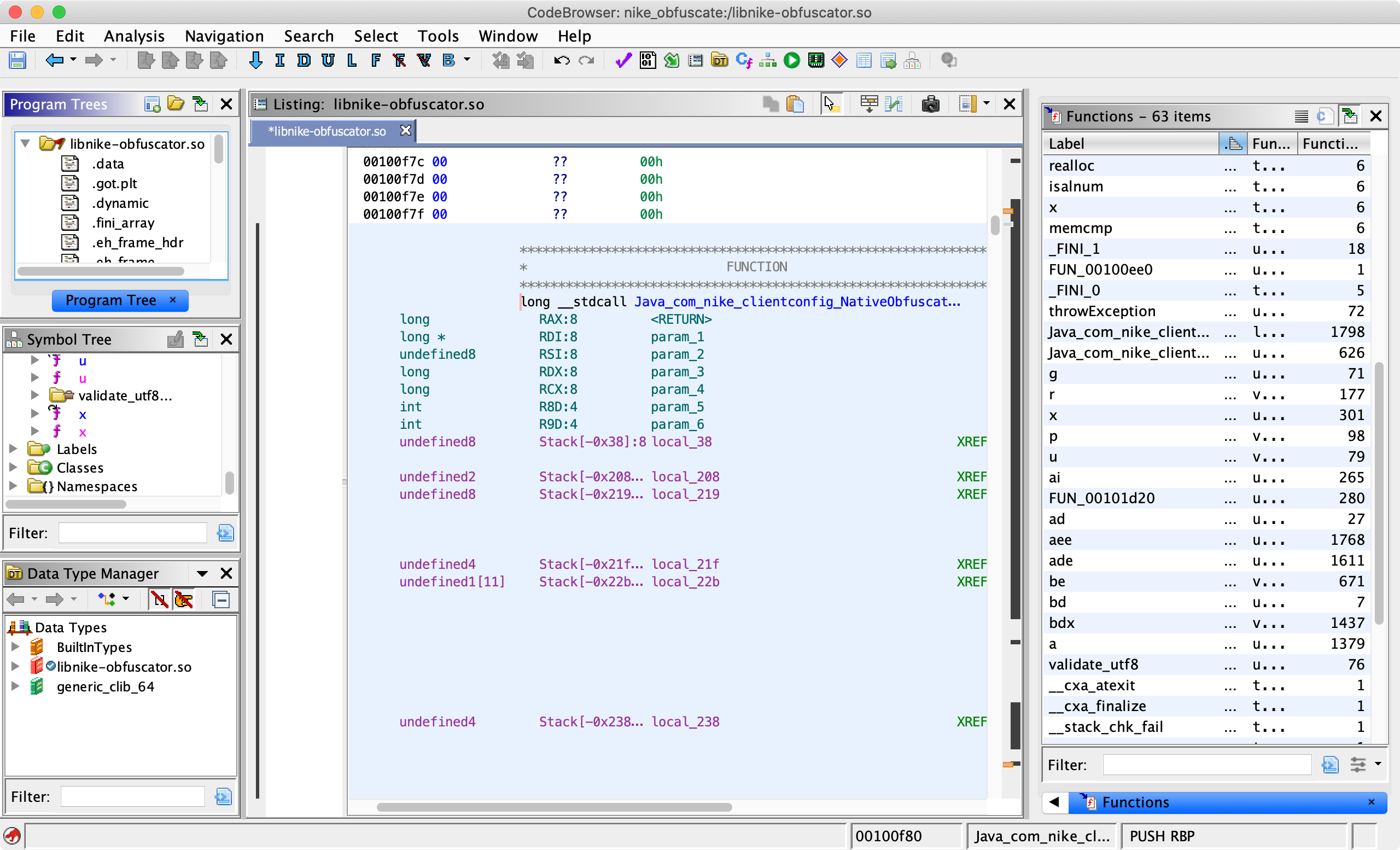
Hi everyone! 👋 If you have been following my blog then you might have already read the article on reverse engineering an Android app by writing custom smali code. I am still very much a reverse engineering beginner so after that article, I got to learn about Frida. I was told that Frida is much faster and a lot easier for scenarios where I want to snoop on functions. Well, I am glad to report that all the suggestions were absolutely correct.

Reverse Engineering Nike Run Club Android App Using Frida - Yasoob Khalid
GitHub - iamsarvagyaa/AndroidSecNotes: An actively maintained, Self curated notes related to android application security for security professionals, bugbounty hunters, pentesters, reverse engineer, and redteamers.
Reverse Engineering Nike Run Club Android App Using Frida - Yasoob Khalid
yasoob (M.Yasoob Ullah Khalid ☺) · GitHub

Rahul Barhate 🎩 🐇 (@d4rw1nk5) / X

Search: [Python] - Liens utiles et à partager

Let's Reverse Engineer an Android App! - Yasoob Khalid
Search: [Python] - Liens utiles et à partager

GitHub - yasoob/nrc-exporter: Download your runs data from Nike Run Club and convert it to GPX format that can be imported in other running apps.
Reverse Engineering Nike Run Club Android App Using Frida - Yasoob Khalid
de
por adulto (o preço varia de acordo com o tamanho do grupo)