Complete UAF exploit - UD Capture
Por um escritor misterioso
Descrição
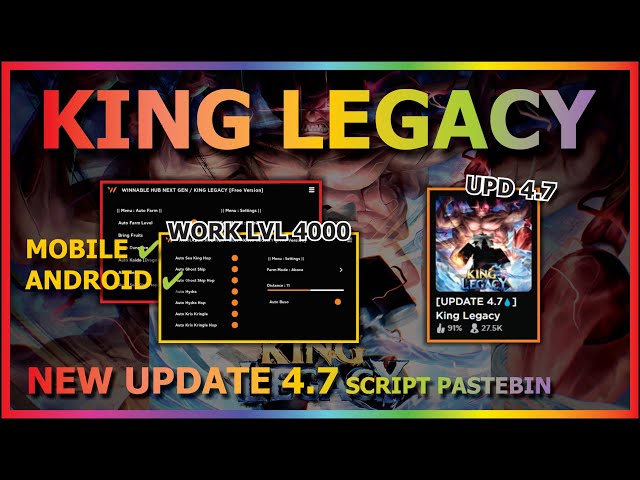
x86 and Secure Software Design 2023 - UD Capture
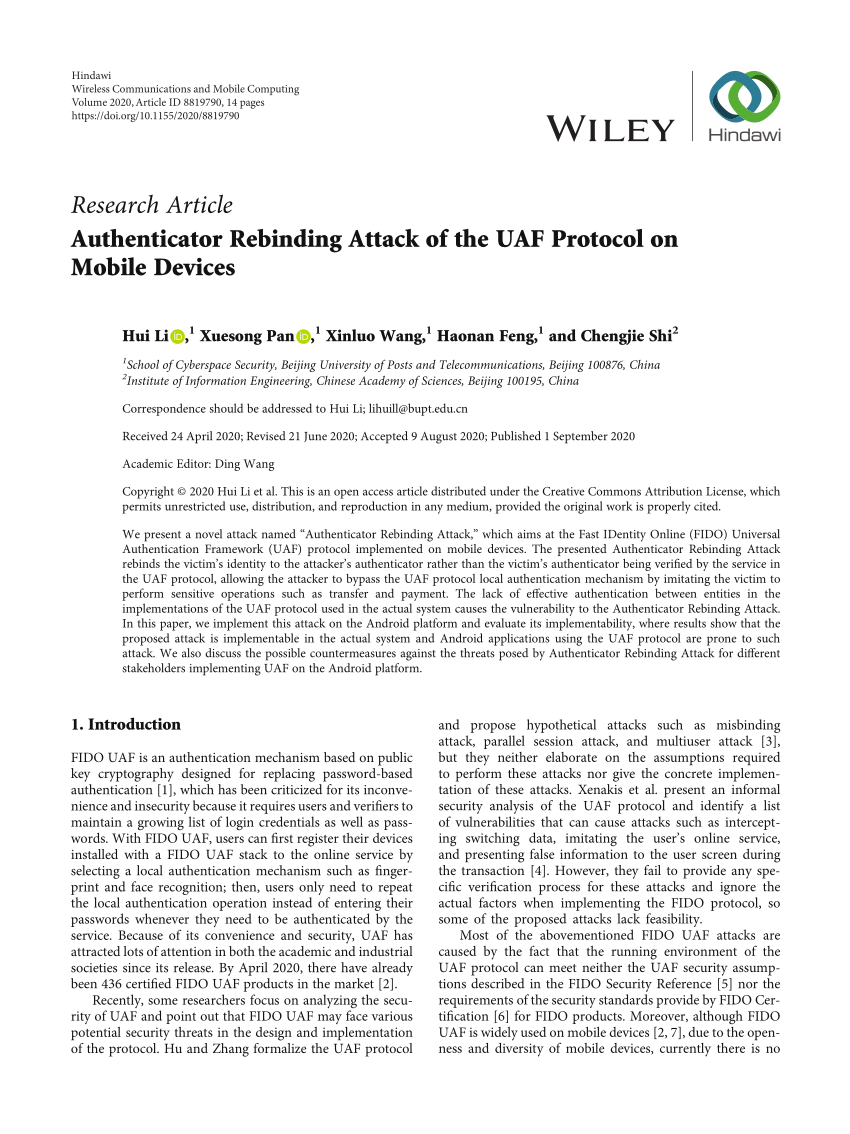
PDF) Authenticator Rebinding Attack of the UAF Protocol on Mobile

Automated Use-After-Free Detection and Exploit Mitigation: How Far

Reverse Engineering Coin Hunt World's Binary Protocol
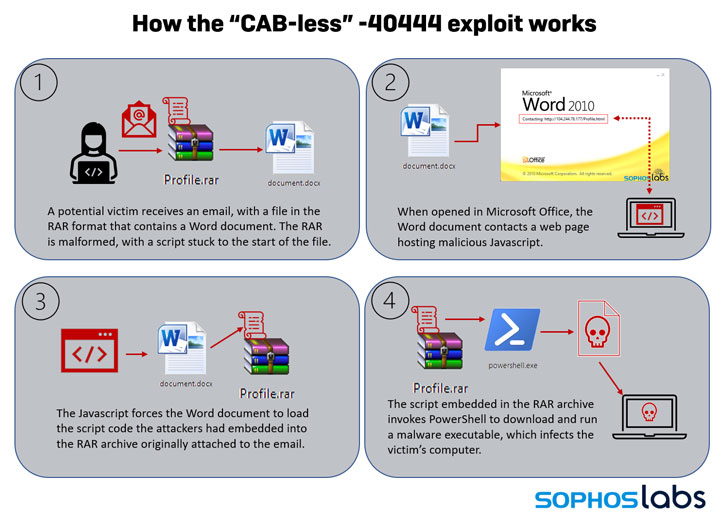
New Exploit Lets Malware Attackers Bypass Patch for Critical
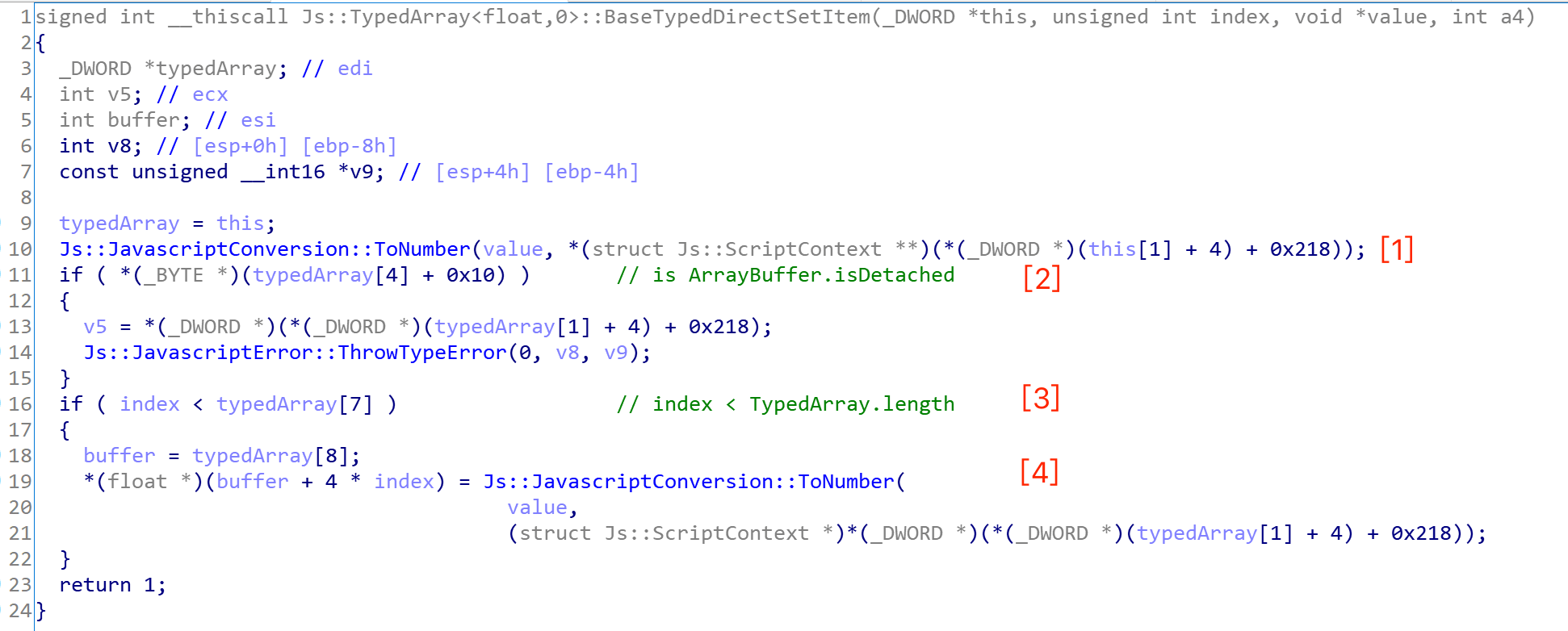
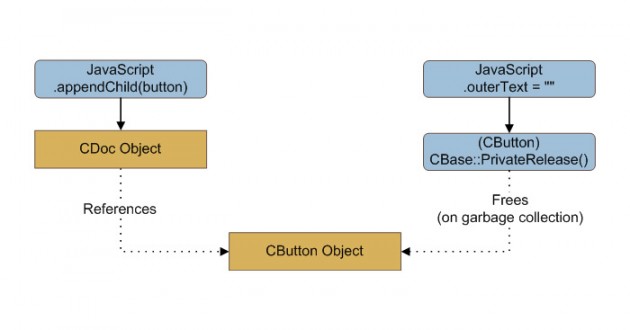
CVE-2020-17053: Use-After-Free IE Vulnerability
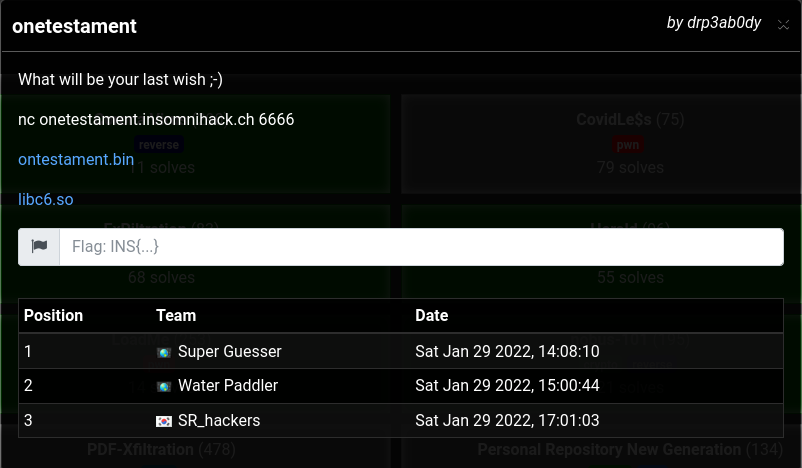
Heap tricks never get old - Insomni'hack teaser 2022
Use-after-frees: That pointer may be pointing to something bad
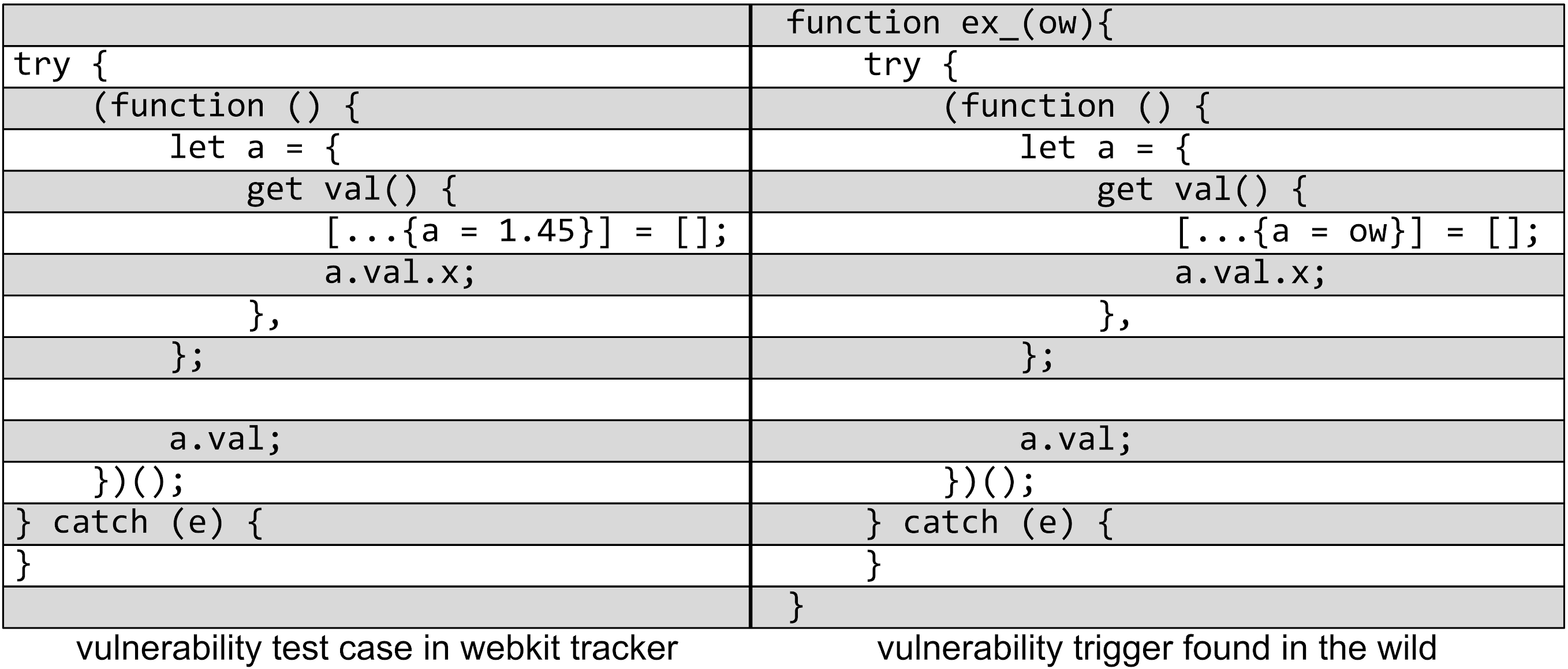
Project Zero: JSC Exploits
de
por adulto (o preço varia de acordo com o tamanho do grupo)