Five Superheroes Who Use Encryption for Good
Por um escritor misterioso
Descrição
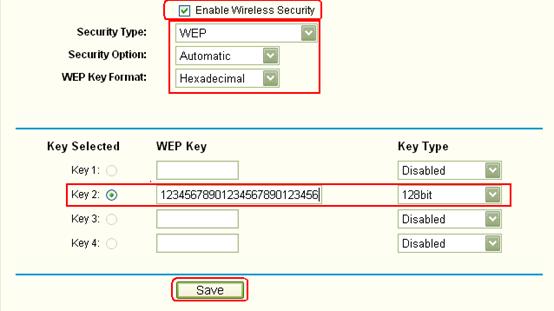
How do I secure my wireless network by using WEP encryption on TP-Link wireless G Router?

What Is Data Encryption: Algorithms, Methods and Techniques

The 6 Most Secure Email Services and the Security Measures They Practice

2: Spectral Analysis of Frequency of Characters of Encrypted data of

The Best Encryption Software for 2023
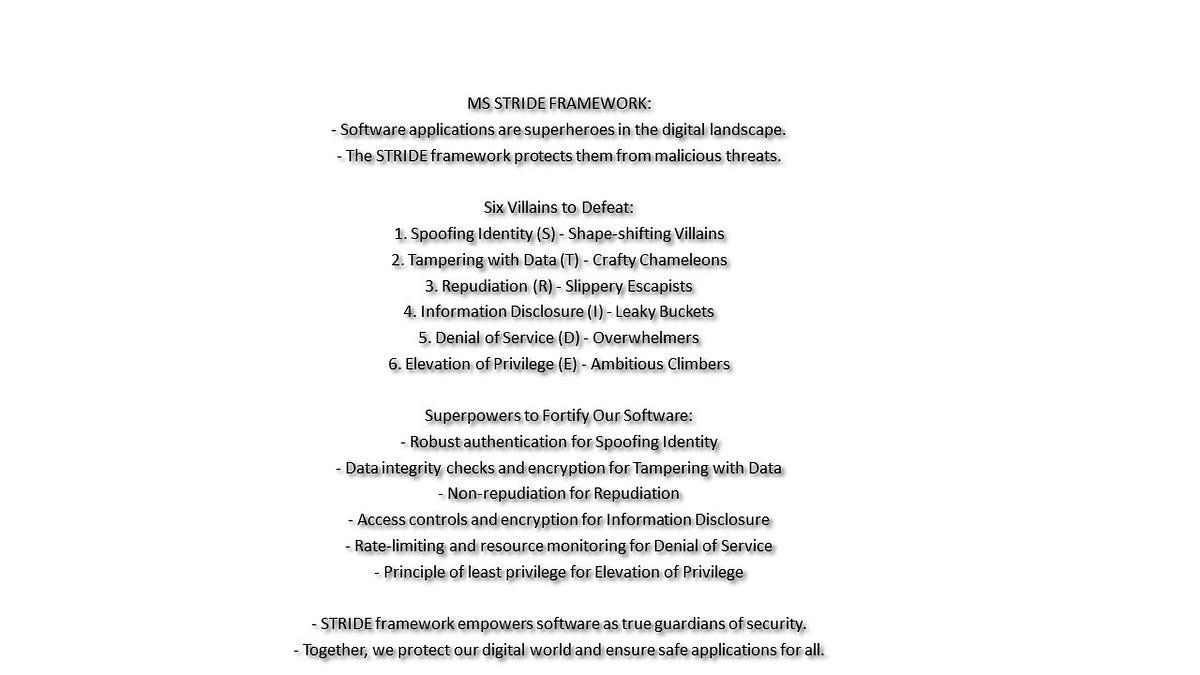
Unraveling the Secrets of STRIDE Framework: Safeguarding Software like a Superhero!, by Goutham Vaidyanathan
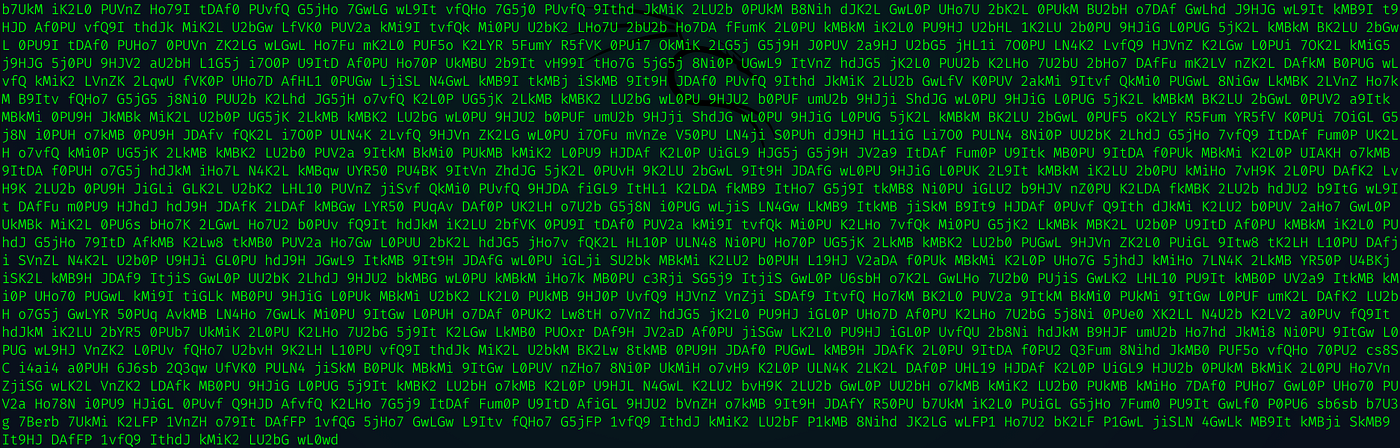
Crypto CTF 2020: Classic Writeup. This is my first time joining a CTF…, by Alexis Lingad

Table of characters after encryption process

Crimeware Trends Ransomware Developers Turn to Intermittent Encryption to Evade Detection - SentinelOne
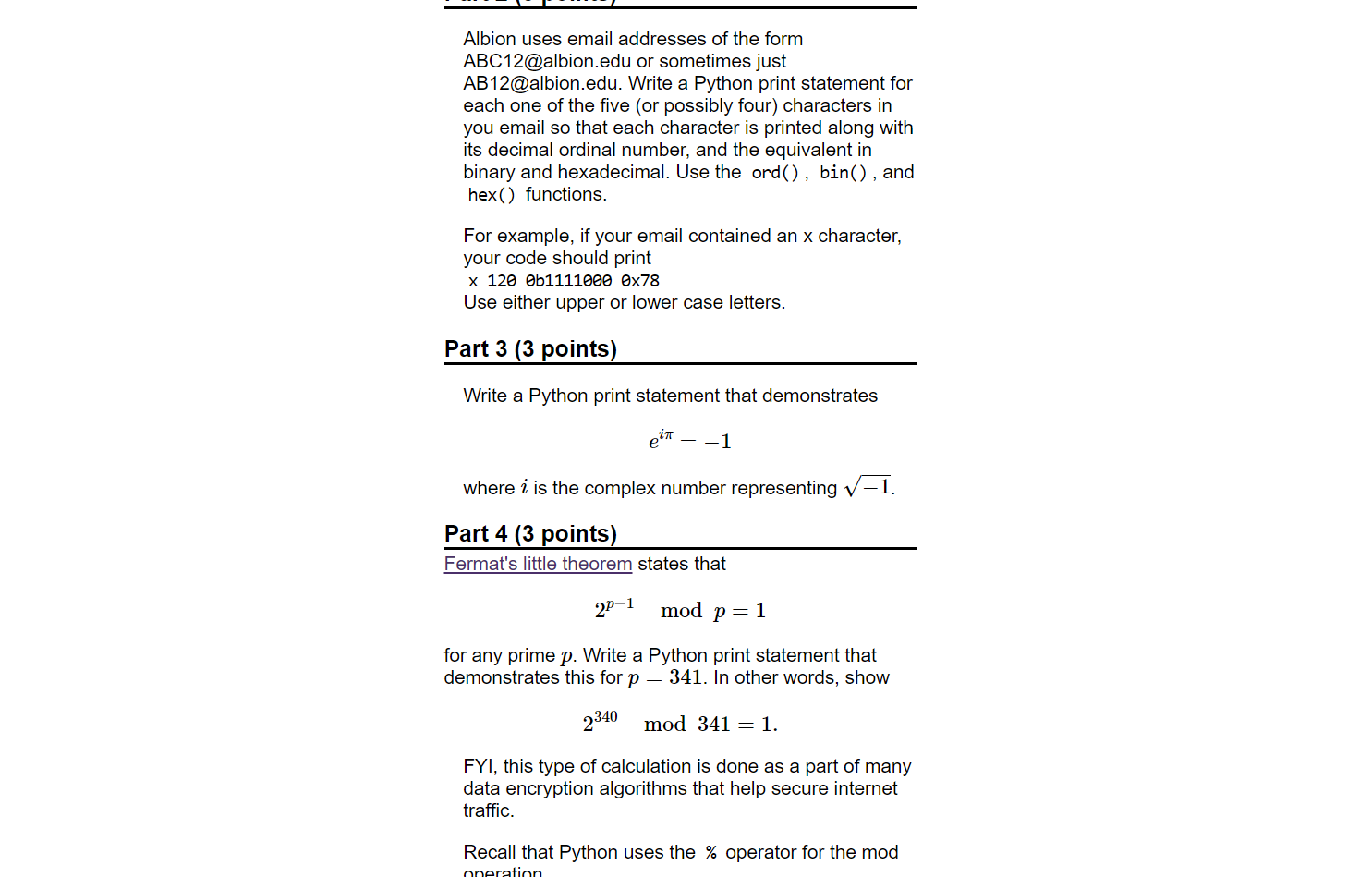
Solved Albion uses email addresses of the form

7 Encryption Methods To Shield Sensitive Data from Prying Eyes
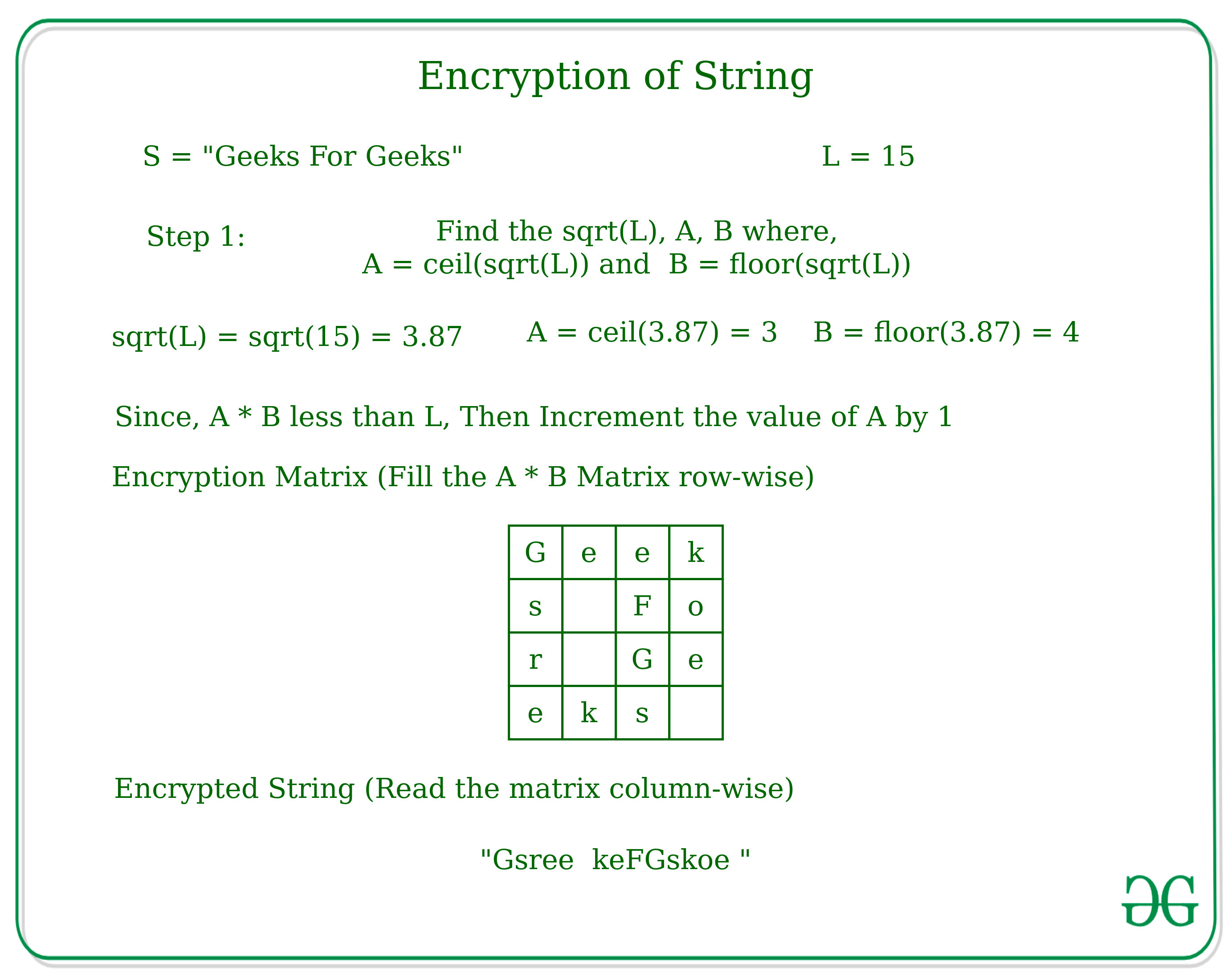
Encryption and Decryption of String according to given technique - GeeksforGeeks
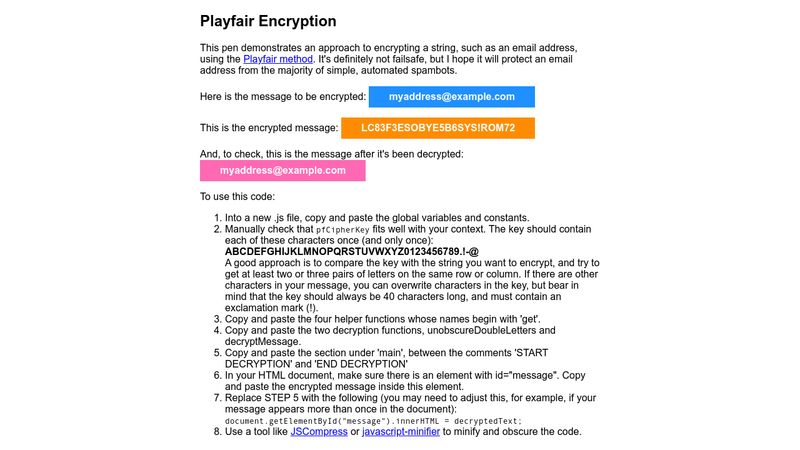
Playfair Encryption

The Unhackable Password: How to Create a Strong and Secure Password Infographic - ThriveDX
de
por adulto (o preço varia de acordo com o tamanho do grupo)