How hackers use idle scans in port scan attacks
Por um escritor misterioso
Descrição
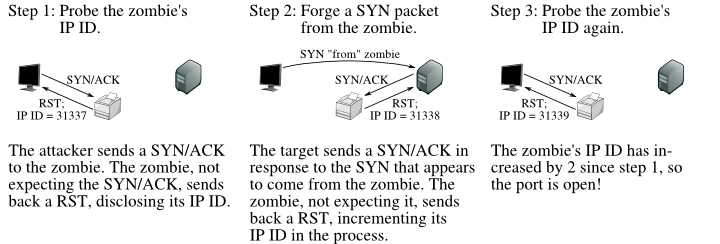
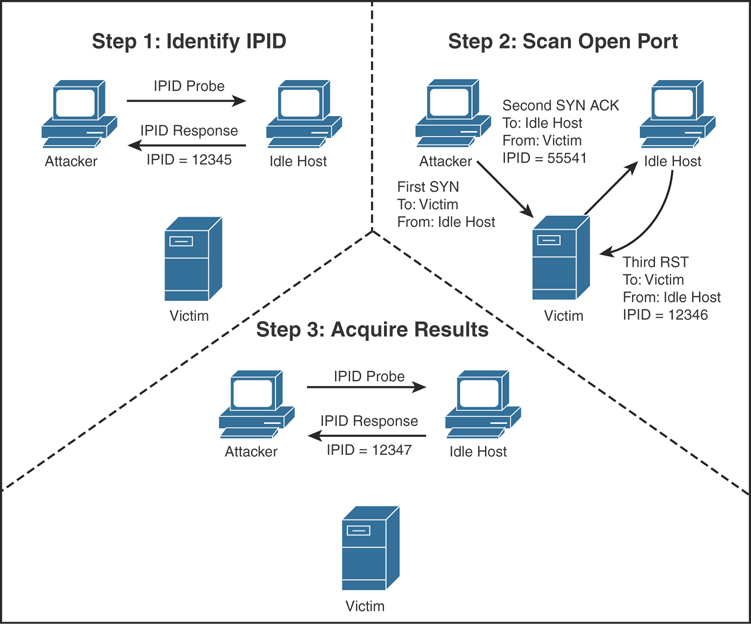
Hackers employ a variety of port scan attacks to gain entry into an enterprise network. Idle scans are a popular method to mask the hacker
Hackers exploit port scan attacks to mask their identities before launching an attack. One of their favorites: the idle scan.
Hackers exploit port scan attacks to mask their identities before launching an attack. One of their favorites: the idle scan.
What is a Cyber Attack? Definition and Related FAQs
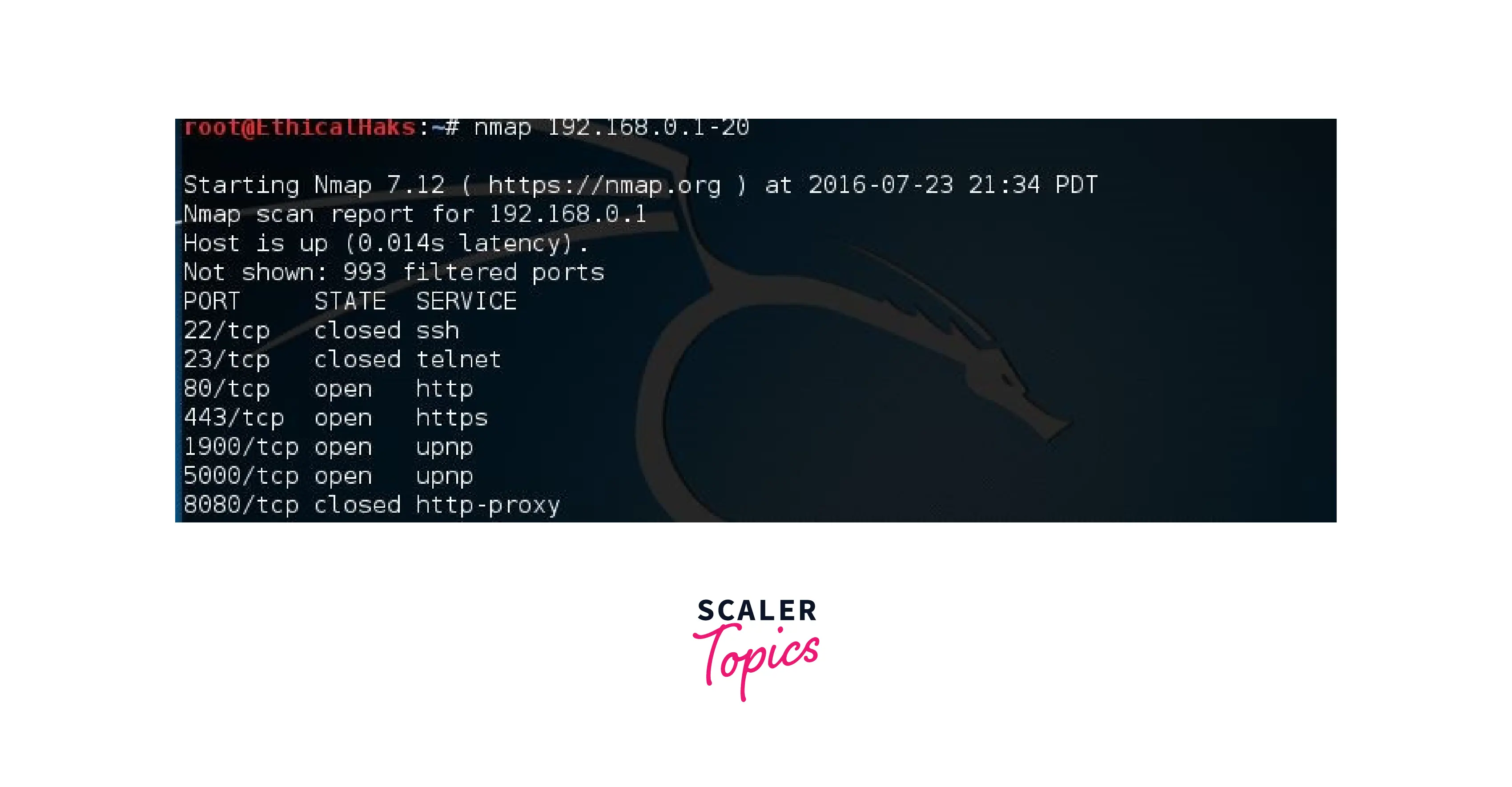
Introduction to Network Auditing with Nmap - Scaler Topics

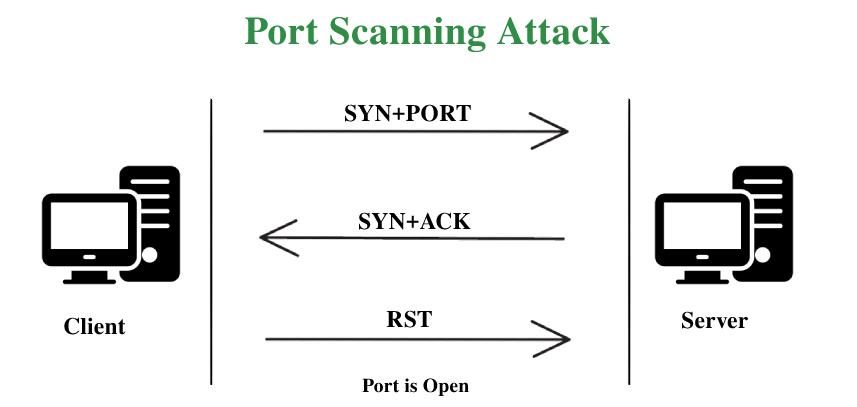
Port Scanning Tutorial for Hackers - Basics

Port Scanning: A Comprehensive Guide for Safeguarding Cyberspace

Idle scan - Wikipedia
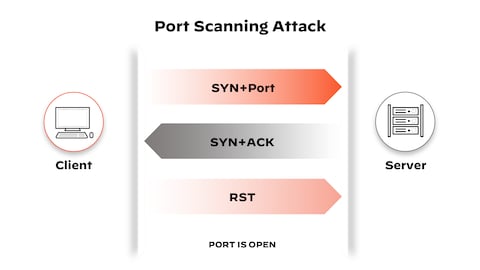
What is a Port Scan? - Palo Alto Networks

Port Scanning: A Comprehensive Guide for Safeguarding Cyberspace
What is Port Scanner? Scanning Ports - ManageEngine OpUtils
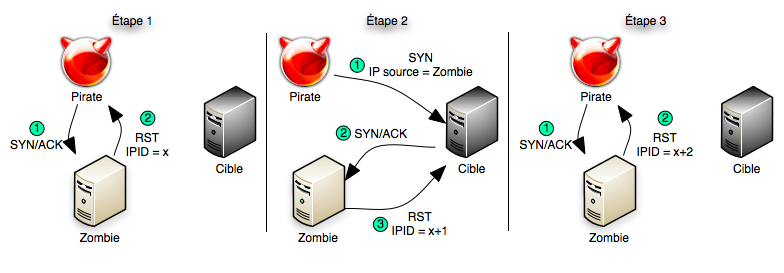
Idle scan - Wikipedia
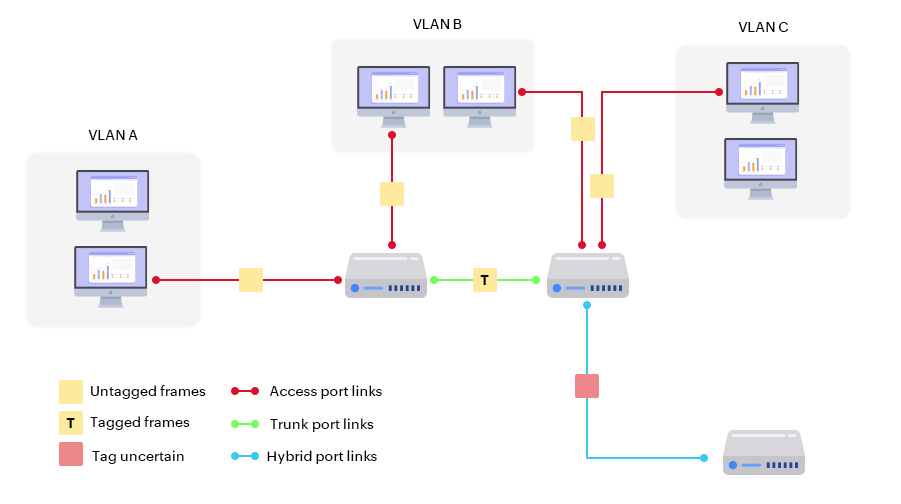
Scanning, Footprinting, Reconnaissance, and Scanning
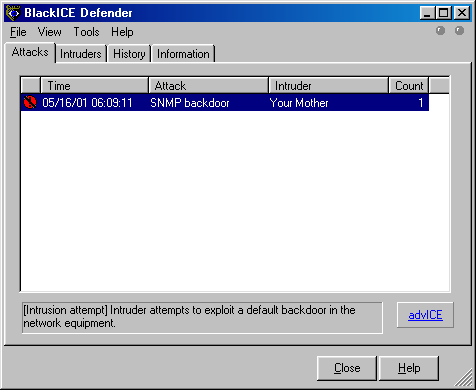
Subverting Intrusion Detection Systems
de
por adulto (o preço varia de acordo com o tamanho do grupo)