Table 2 from Malware Detection and Removal: An examination of personal anti-virus software
Por um escritor misterioso
Descrição
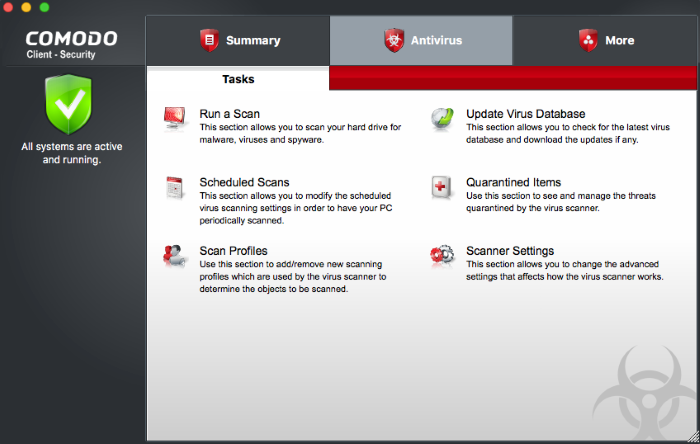
Antivirus Tasks - Introduction, Antivirus Scans, Comodo Client

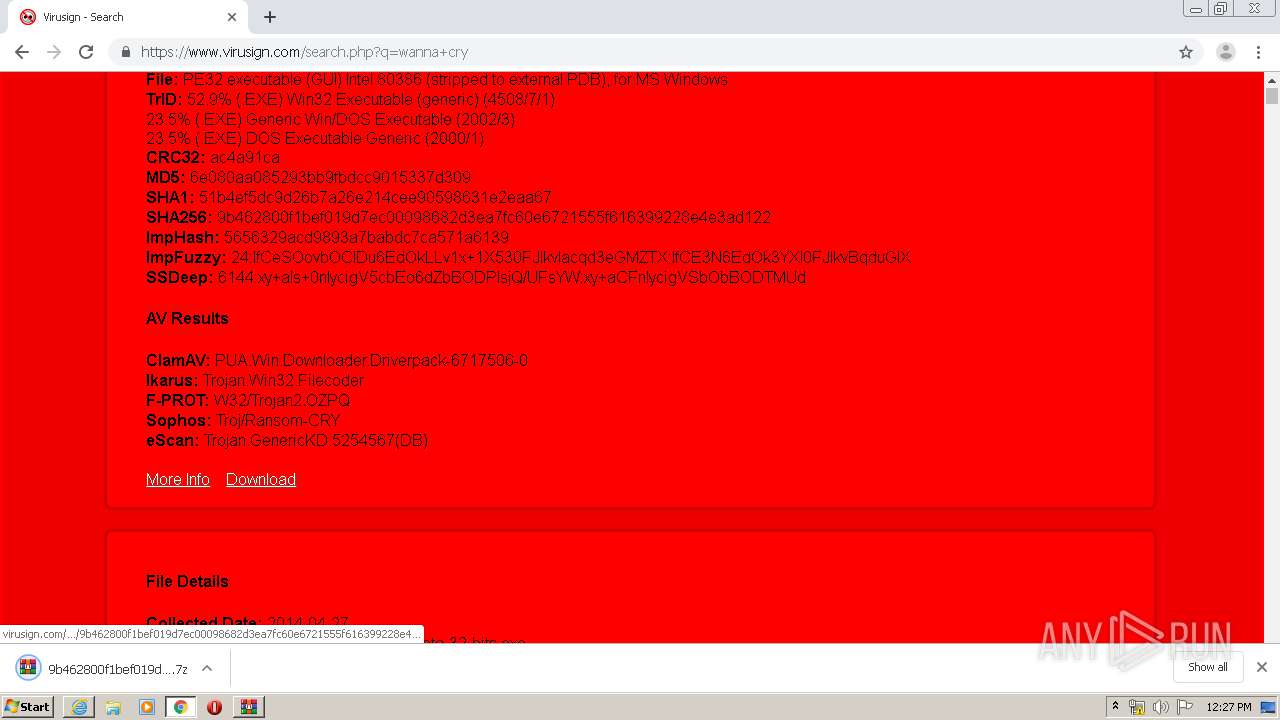
Malware Detection in Executables Using Neural Networks
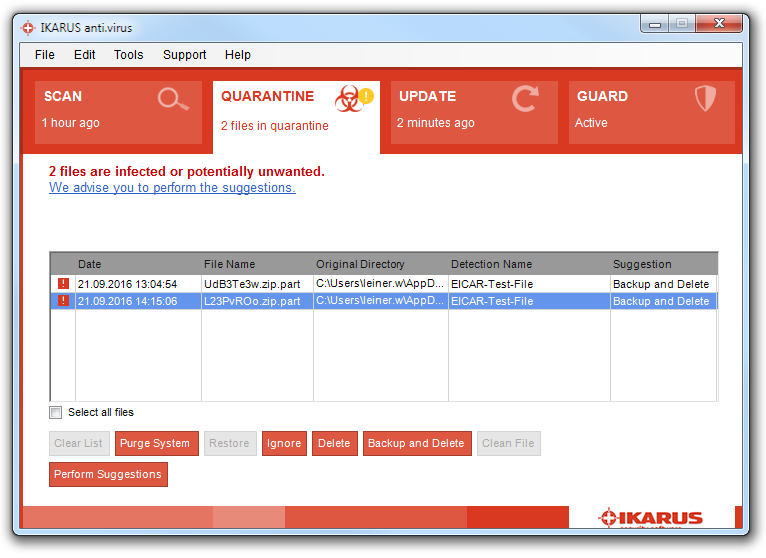
Comparative Performance Analysis of Anti-virus Software

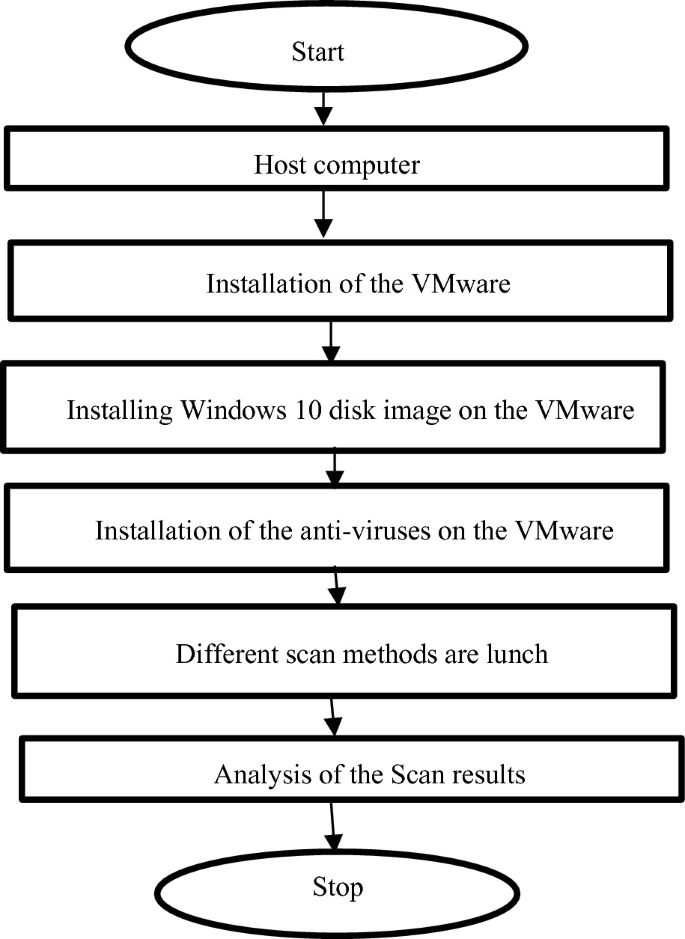
A flow chart of malware detection approaches and features
Most Common Malware Attacks

What Is Malware? Definition, Types, Removal Process, and

Table 2 from Malware Detection and Removal: An examination of

What is an antivirus product? Do I need one?

9 types of malware and how to recognize them
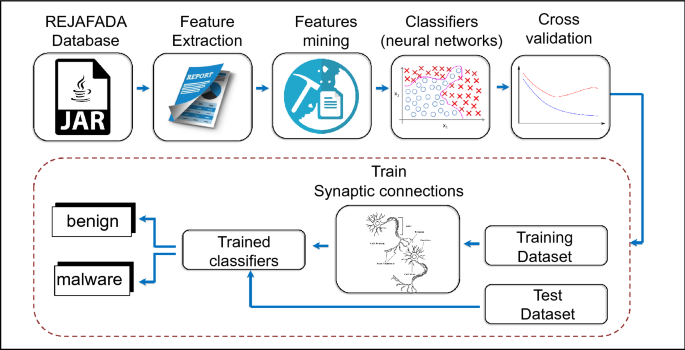
Antivirus applied to JAR malware detection based on runtime

Malware Detection flowchart [64]
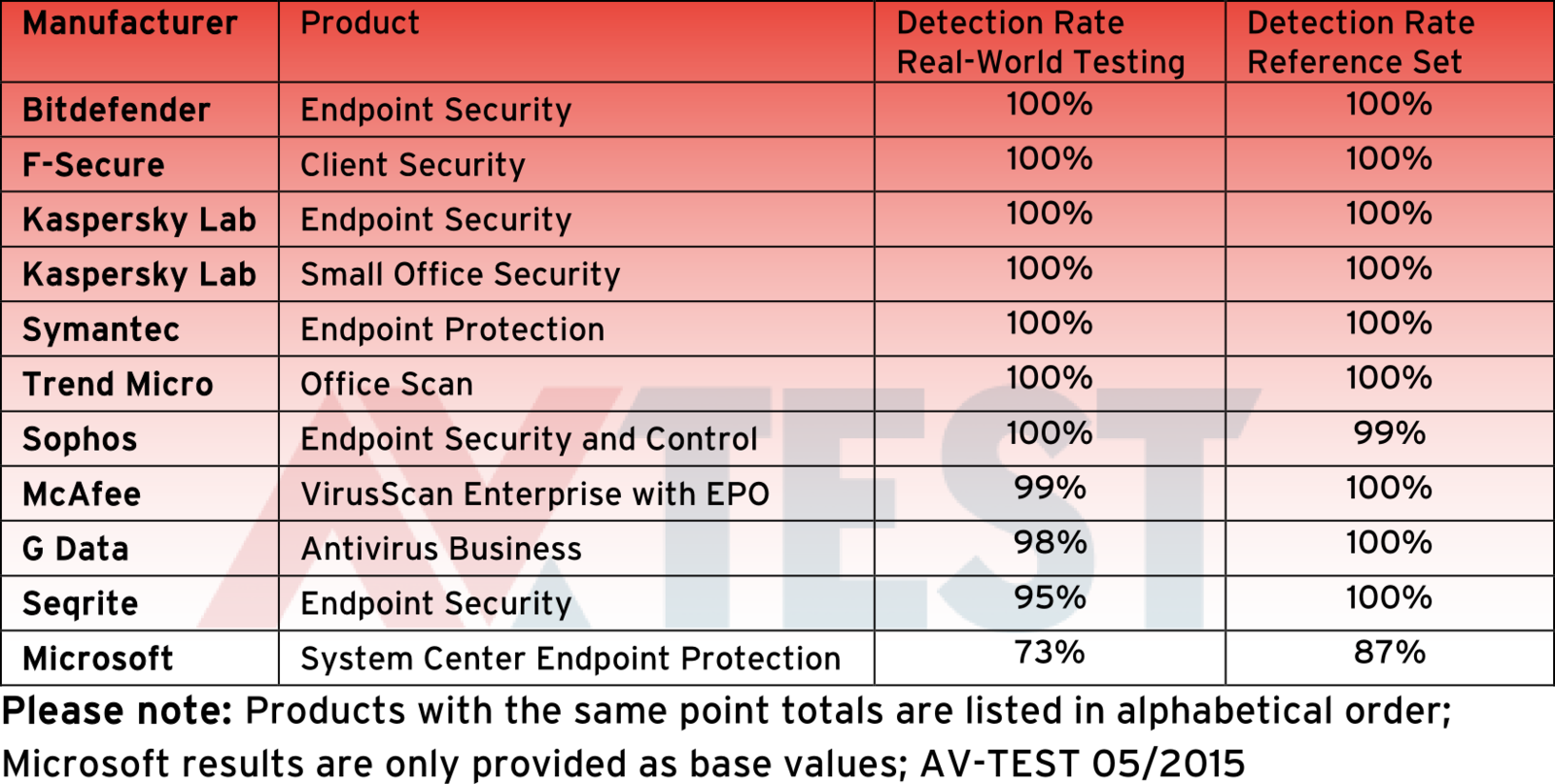
Microsoft security tool fails malware detection test
de
por adulto (o preço varia de acordo com o tamanho do grupo)