Malware analysis Malicious activity
Por um escritor misterioso
Descrição

Info stealers and how to protect against them

Malware Analysis: Steps & Examples - CrowdStrike

Routers Roasting on an Open Firewall: the KV-botnet Investigation
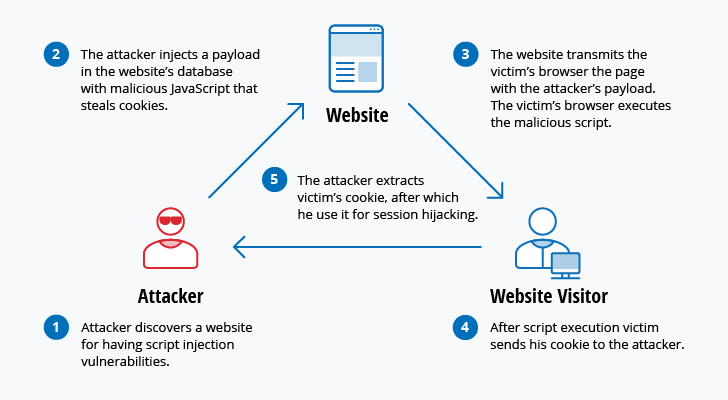
The 12 Most Common Types of Cybersecurity Attacks Today
10 Best Antivirus Software in 2023: Windows, Android, iOS, Mac

Patch Now: Exploit Activity Mounts for Dangerous Apache Struts 2 Bug

Playbook of the Week: Malware Investigation and Response - Palo

Remediation and Malware Detection Overview

Playbook for Malware outbreak

AlienVault - Open Threat Exchange

Malware analysis index.html Malicious activity

Malware analysis file Malicious activity

Building A Simple Malware Analysis Pipeline In The Homelab Pt - 1
de
por adulto (o preço varia de acordo com o tamanho do grupo)