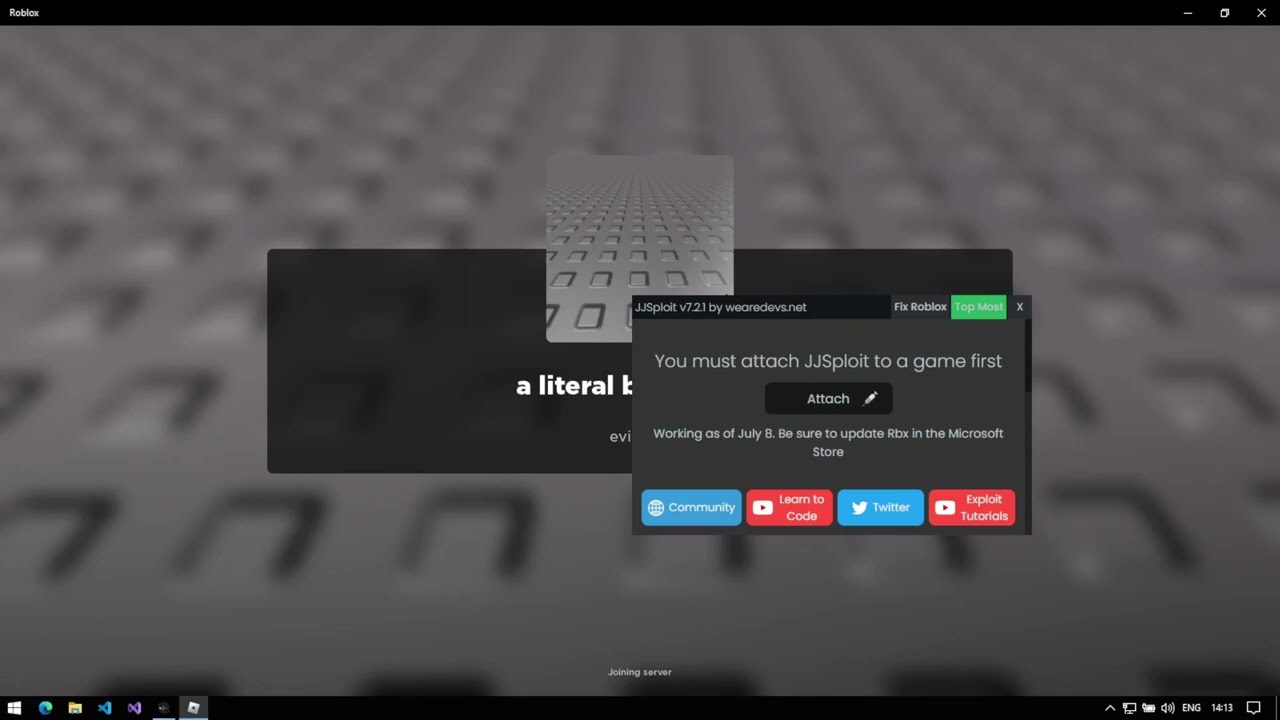
Malware analysis Malicious activity
Por um escritor misterioso
Descrição
Malware analysis Malicious activity

Malware Analysis: Steps & Examples - CrowdStrike

FBI, CISA, MS-ISAC release cybersecurity advisory on emerging Rhysida ransomware targeting critical sectors - Industrial Cyber

Cybersecurity Search Engine

Rising threats: Cybercriminals unleash 411,000 malicious files daily in 2023

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

Playbook for Malware outbreak

Endpoint Detection and Response, Free - What is EDR Security?

Malware analysis index.html Malicious activity

Feature Extraction and Detection of Malwares Using Machine Learning

How to Do Malware Analysis?

Intro to Malware Analysis: What It Is & How It Works - InfoSec Insights

Building A Simple Malware Analysis Pipeline In The Homelab Pt - 1 · Arch Cloud Labs
de
por adulto (o preço varia de acordo com o tamanho do grupo)