Phishing Analysis. Ojectives Phishing Internet Protocol (IP) addresses Domain Name System (DNS) names Analyse “From” addresses Analyse URL's Trace the. - ppt download
Por um escritor misterioso
Descrição
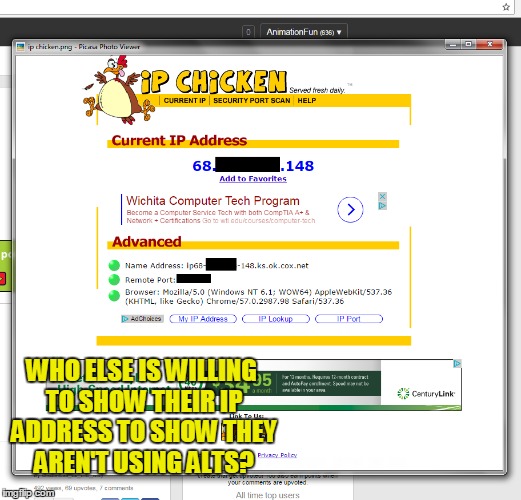
Phishing utilizing social engineering Induces the recipient to reveal desired personal information Bank account SSN Address Etc. Sometimes entices the recipient to go to a malicious web site
Summary IANA assigns IP addresses Regional Registries assign addresses for regions Start with ARIN when researching –ARIN will tell you where to go for non- American addresses Turn on long headers in Don t fall for silly stuff in the body of the
Summary IANA assigns IP addresses Regional Registries assign addresses for regions Start with ARIN when researching –ARIN will tell you where to go for non- American addresses Turn on long headers in Don t fall for silly stuff in the body of the
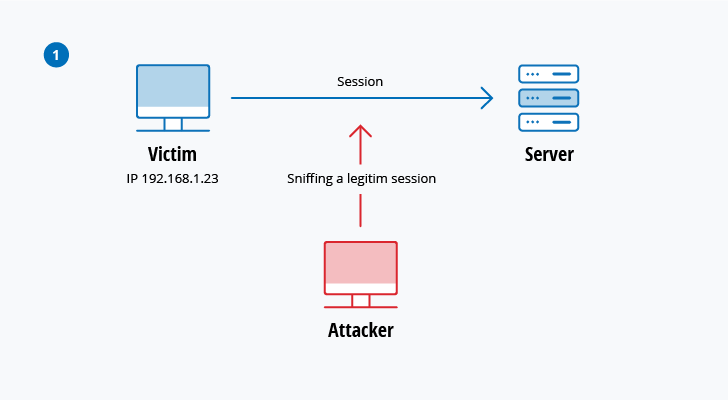
The 12 Most Common Types of Cybersecurity Attacks Today

Cyber Security - The Driz Group Official Blog - The Driz Group
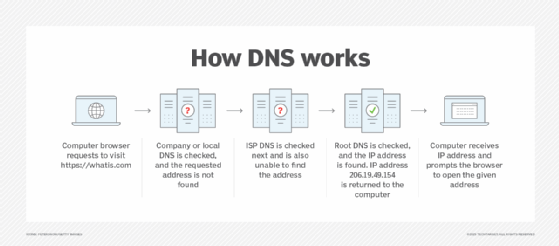
What is cache poisoning and how does it work?

The COVID‐19 scamdemic: A survey of phishing attacks and their
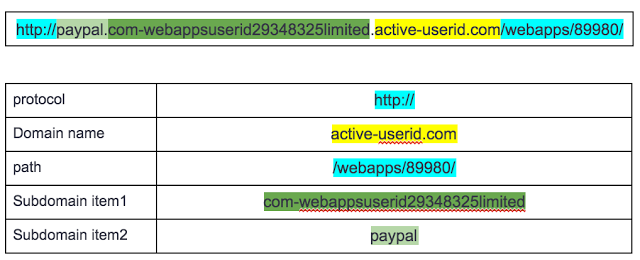
Phishing URL Detection with ML. Phishing is a form of fraud in
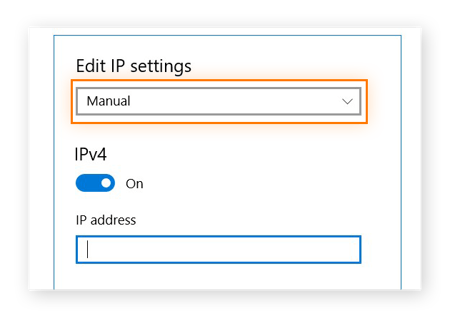
Static vs. Dynamic IP Addresses: What's the Difference?

Computer security - Wikipedia
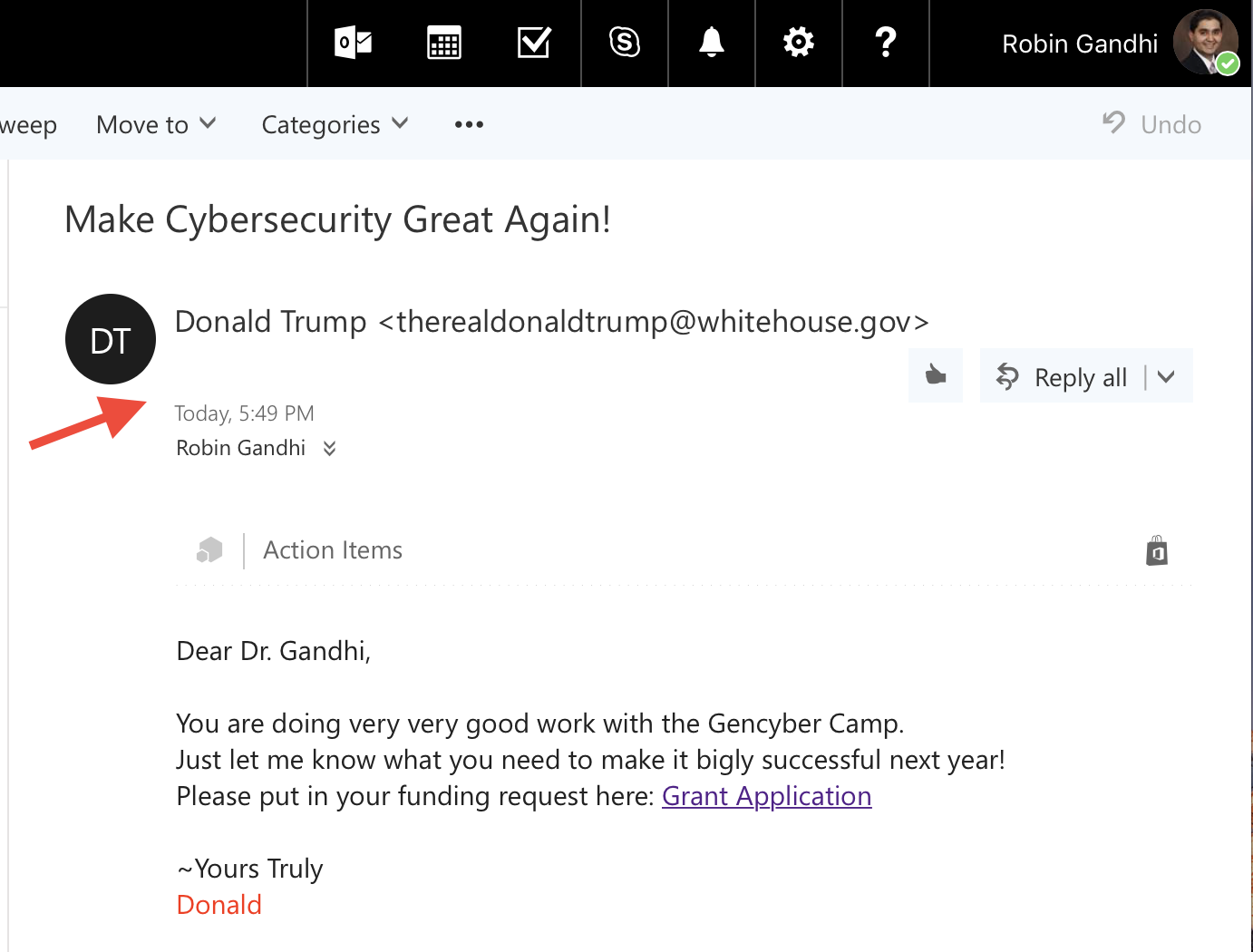
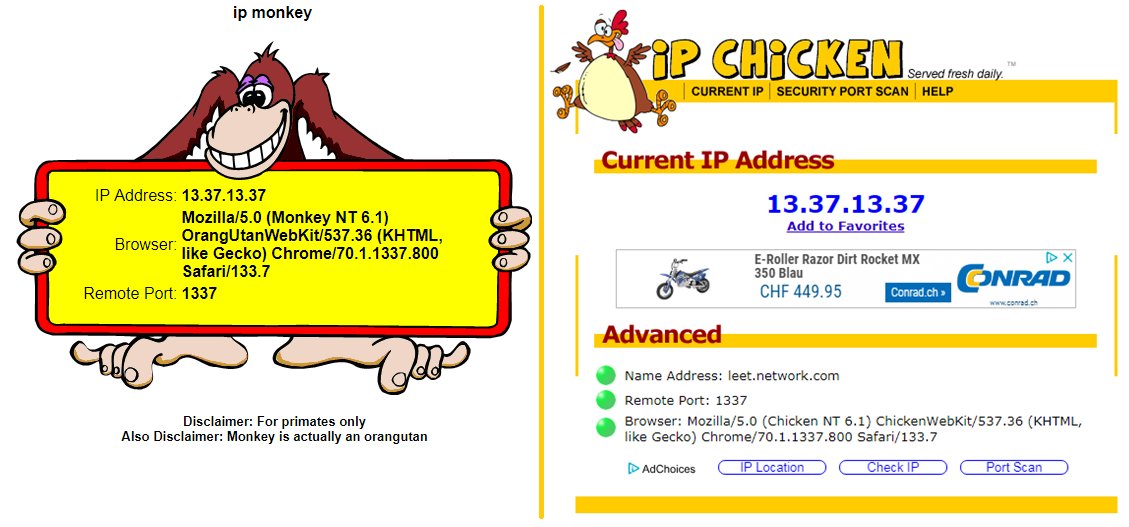
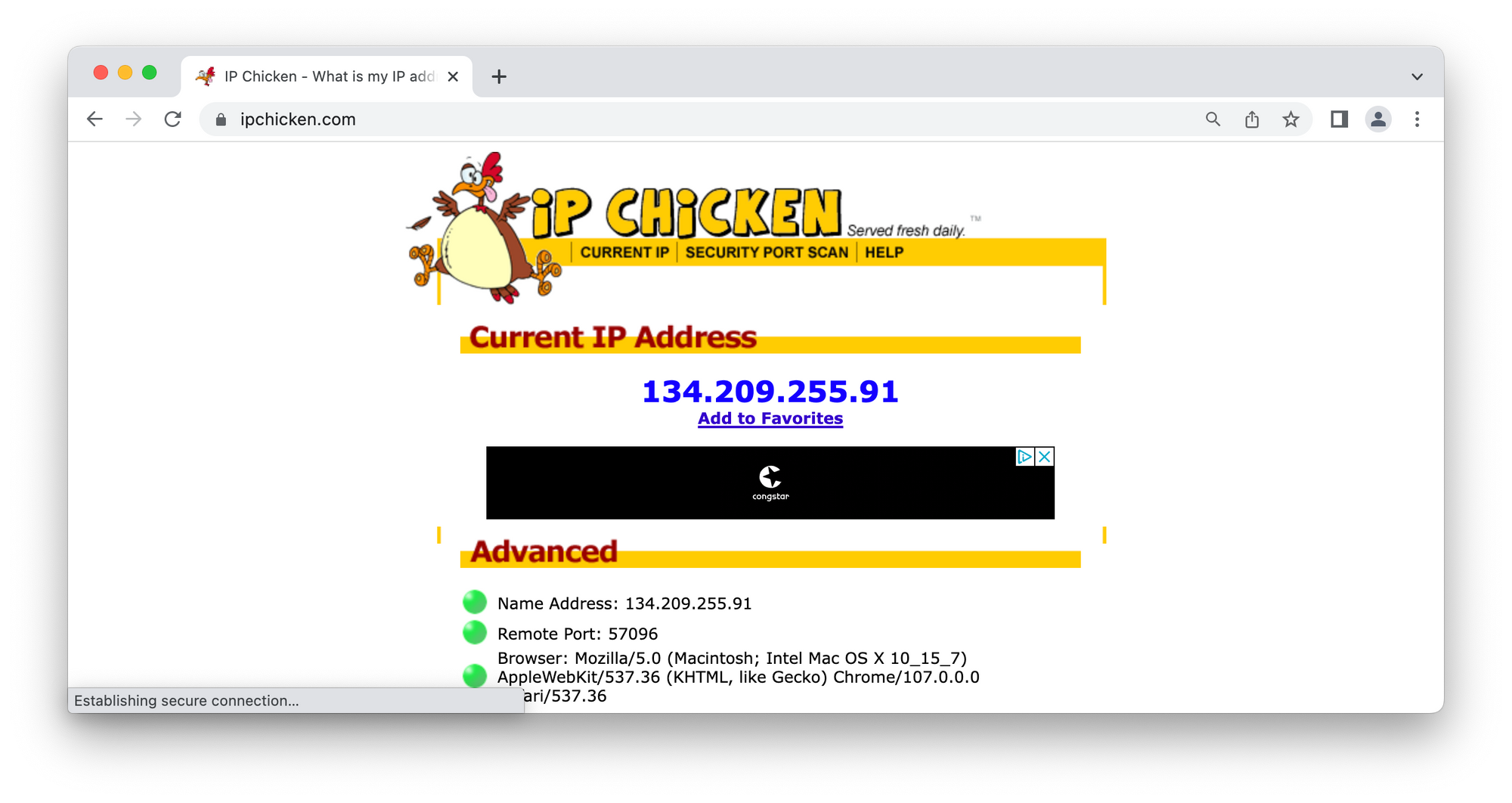
Phishing - Email Header Analysis · nebraska-gencyber-modules
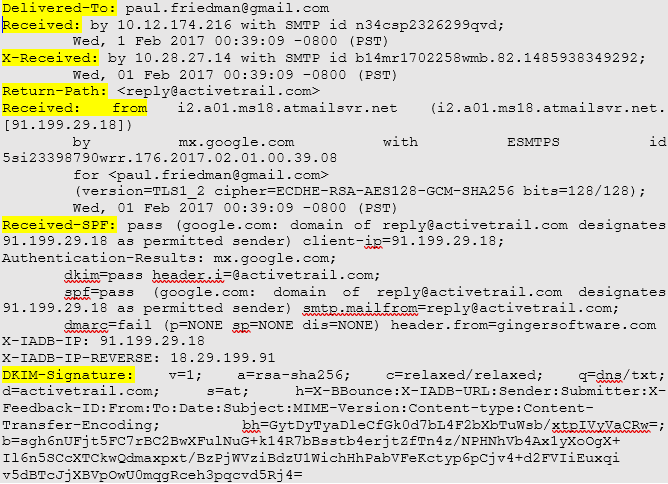
Email Forensics Investigation Techniques- A Complete Guide
de
por adulto (o preço varia de acordo com o tamanho do grupo)


:max_bytes(150000):strip_icc():focal(399x0:401x2)/dr-nowzaradan-f09a4ca873684553b2fa16bb0d289460.jpg)
