Hack Like a Pro: How to Remotely Grab a Screenshot of Someone's Compromised Computer « Null Byte :: WonderHowTo
Por um escritor misterioso
Descrição
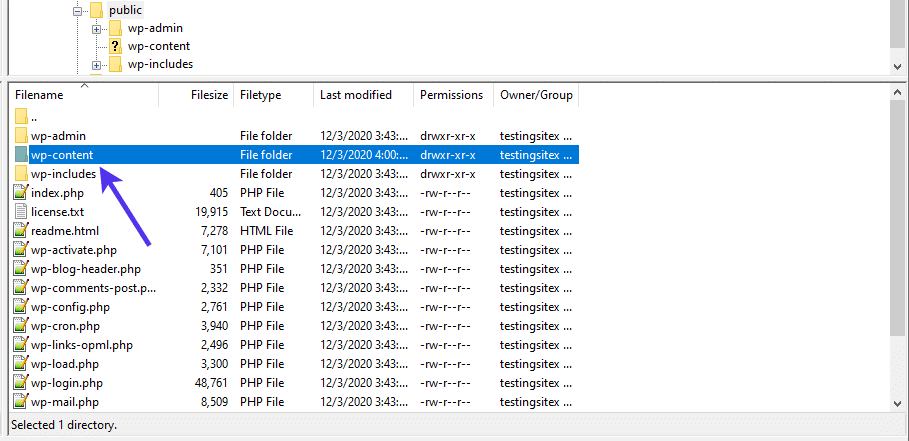
A Comprehensive Guide on WordPress Files and How to Use Them
Hack Lets You Fully Activate a Bootleg Copy of Windows 8 Pro for Free « Windows Tips :: Gadget Hacks

Gadget Hacks » Smartphone Lifehacks, Guides, Tips, Tricks & How-Tos

Opinion: There's a Blind Spot in Augmented Reality, and the Clarifying Lens of Crypto Is the Prescription, Here's Why « Next Reality

The hackers manual 2015 revised edition by Gerson Villa Gonzalez - Issuu
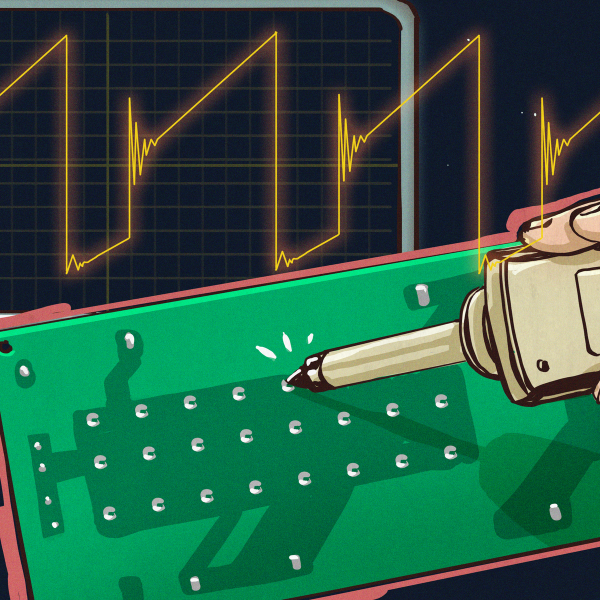
Hackaday Fresh Hacks Every Day

Find Vulnerable Services & Hidden Info Using Google Dorks [Tutorial]

A Comprehensive Guide on WordPress Files and How to Use Them

Find Vulnerable Services & Hidden Info Using Google Dorks [Tutorial]

Pentetration Testing, PDF, Security Hacker

Paper id 311201535

Hack WPA/WPA2 PSK Capturing the Handshake - Kali Linux Hacking Tutorials
de
por adulto (o preço varia de acordo com o tamanho do grupo)