Vulnerability Scanning in your CI/CD Pipeline - Part Two
Por um escritor misterioso
Descrição
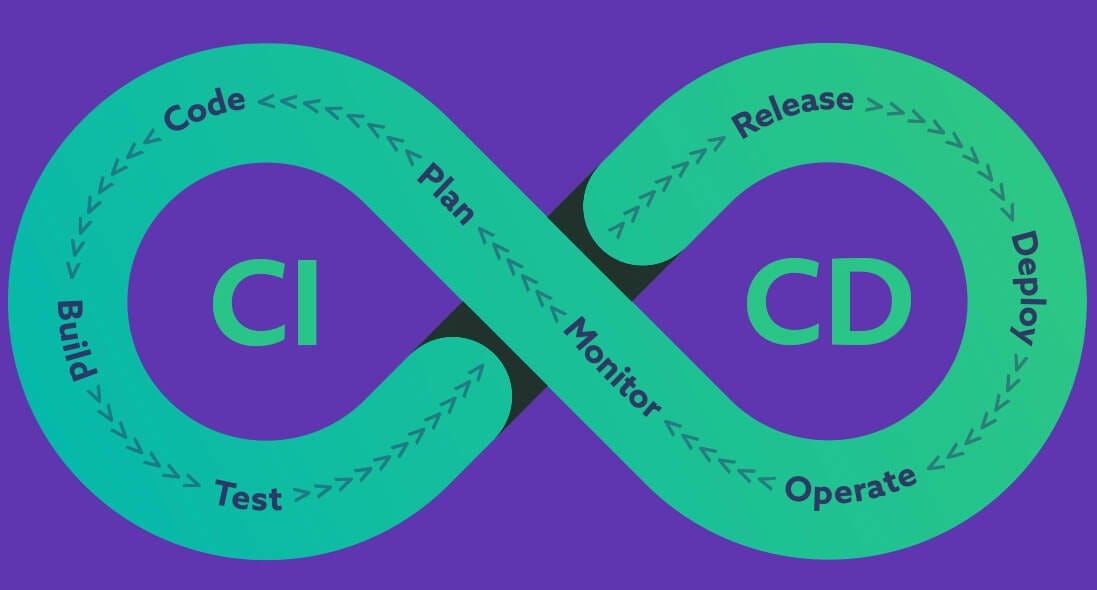
Getting Started With CI/CD Pipeline Security
Building a security-conscious CI/CD pipeline, by Snyk

Enhance your CI/CD deployment by using Vulnerability Assessments from Azure Defender for ACR – Azure Aggregator
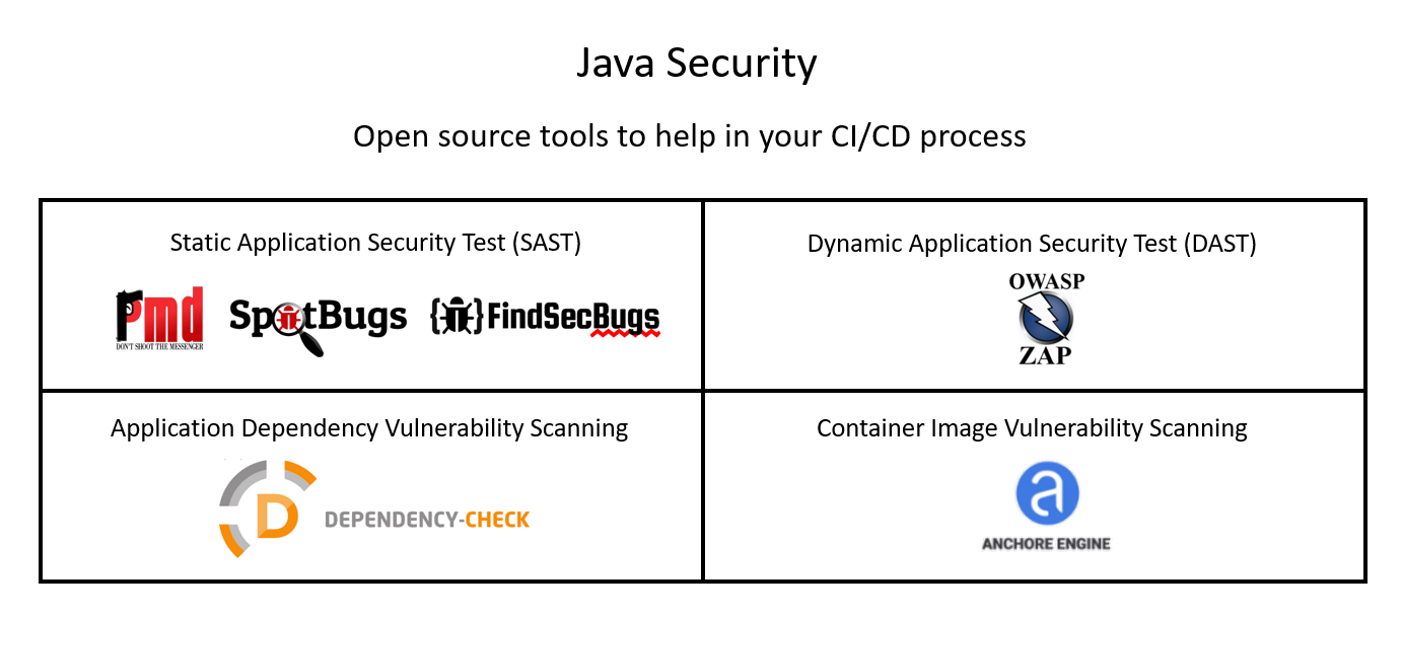
Java Security: Open Source tools for use in CI/CD pipelines
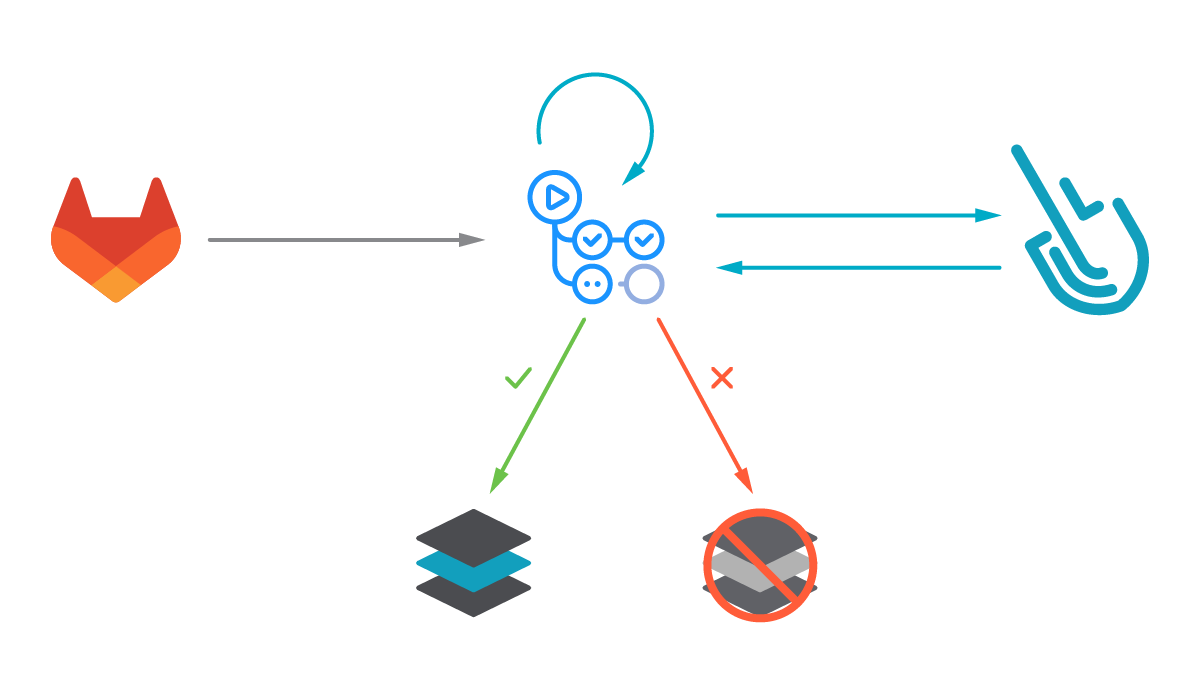
Image scanning for GitLab CI/CD – Sysdig

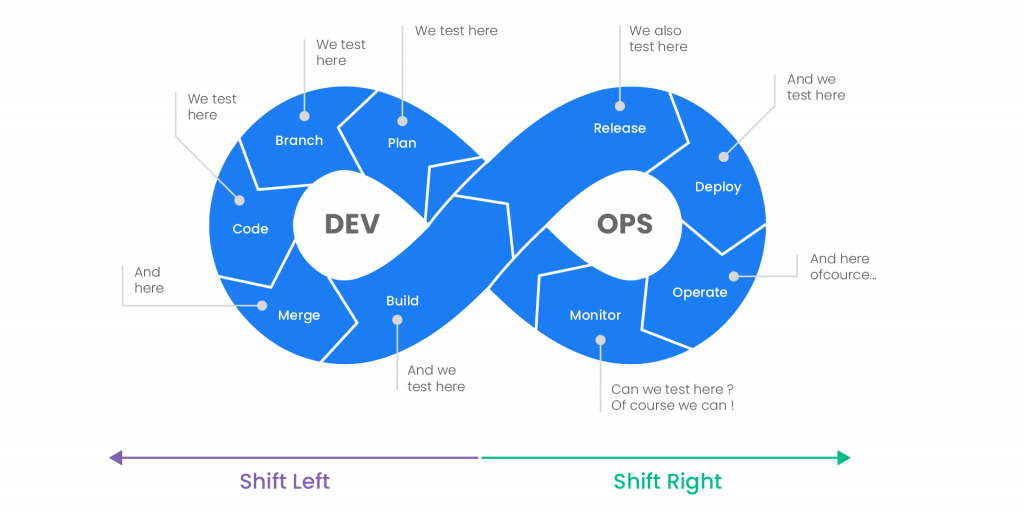
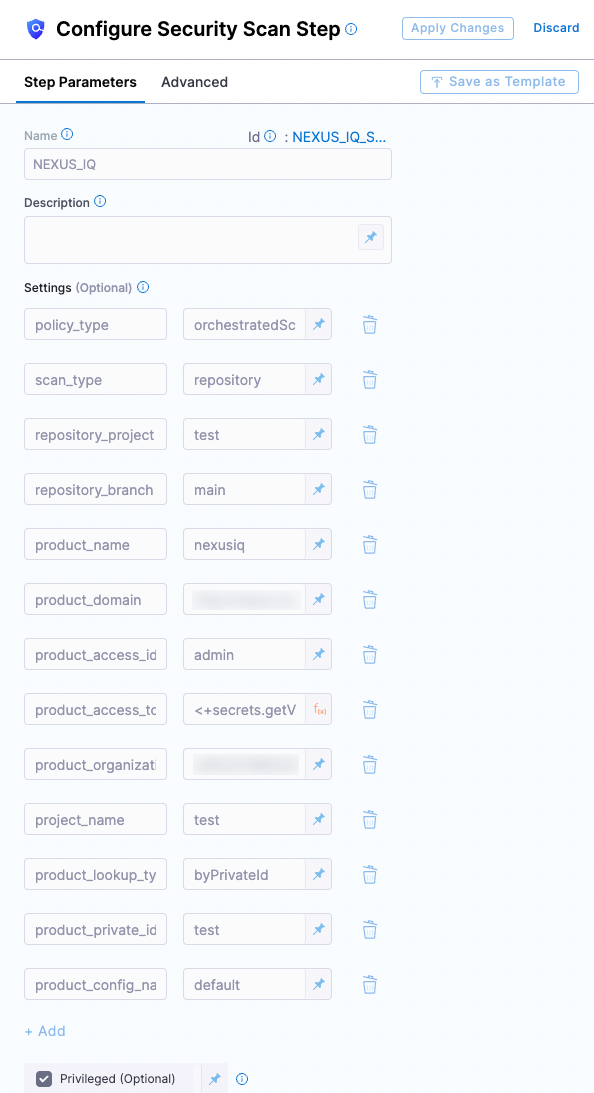
CI/CD Pipeline Security in DevSecOps

8 tips for securing your CI/CD pipeline with Snyk
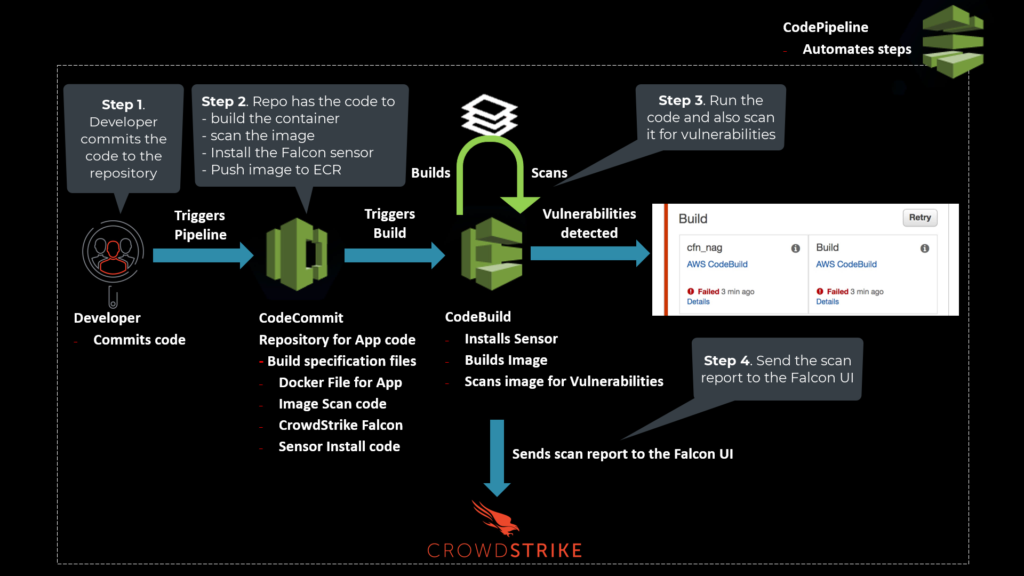
Shifting Left with the CrowdStrike and AWS CI/CD Pipeline

Integrate Security and Compliance into Your CI/CD Pipeline - The New Stack
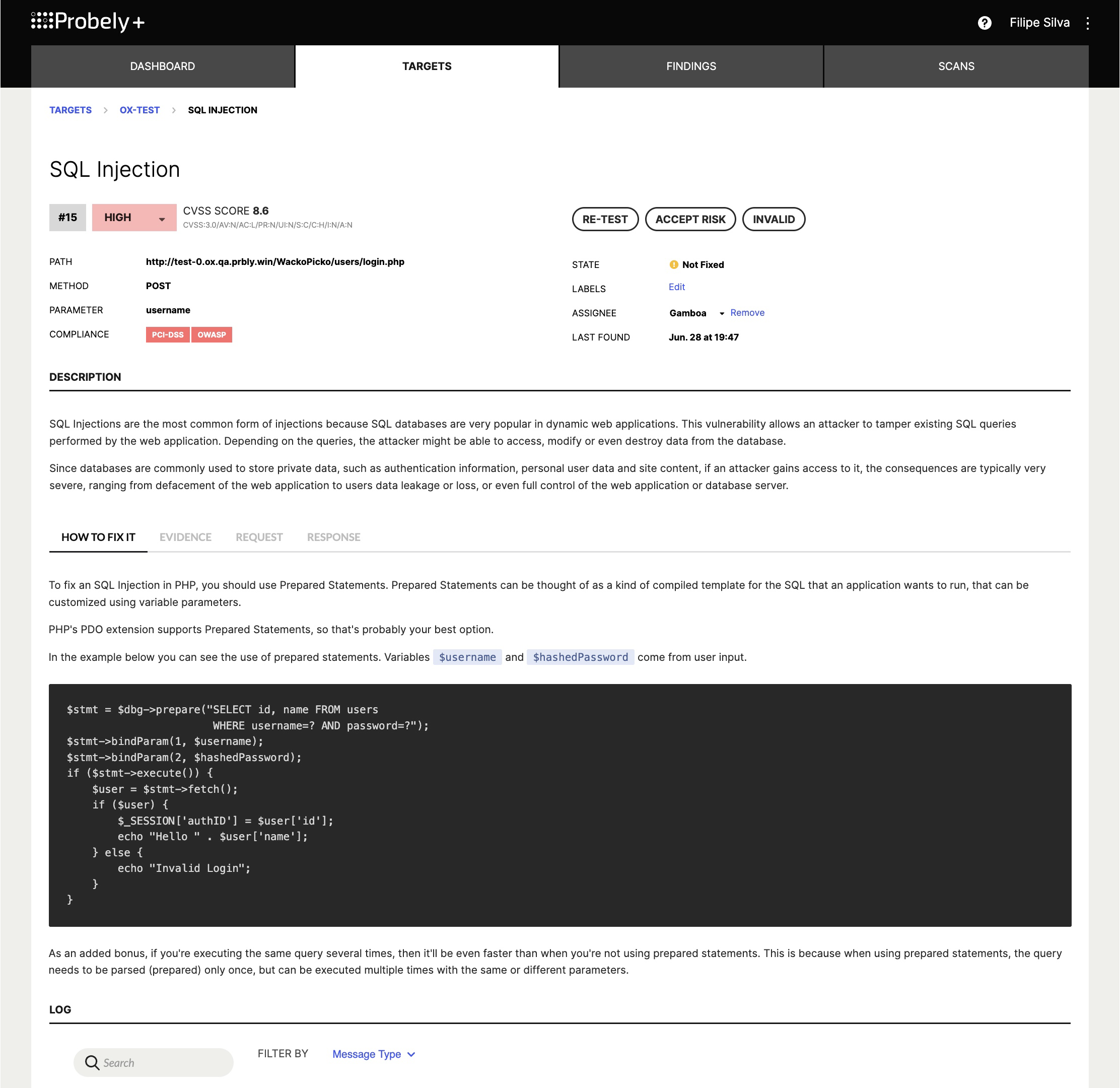
Integrating Web Vulnerability Scanners in Continuous Integration: DAST for CI/CD — Probely
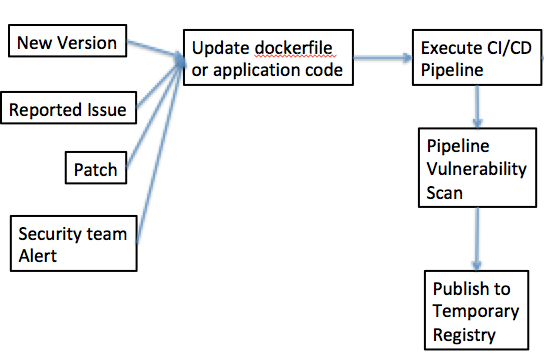
Pipeline Vulnerability Scanner - Cloud Adoption Patterns

Implement DevSecOps to Secure Your CI/CD Pipeline

CI/CD Security Best Practices

Top 5 Considerations for Better Security in Your CI/CD Pipeline (sold in package, 10pc per package)
de
por adulto (o preço varia de acordo com o tamanho do grupo)


/cdn.vox-cdn.com/uploads/chorus_image/image/71912798/Bella_Ramsey__Anna_Torv___Liane_Hentscher_HBO.0.jpg)

